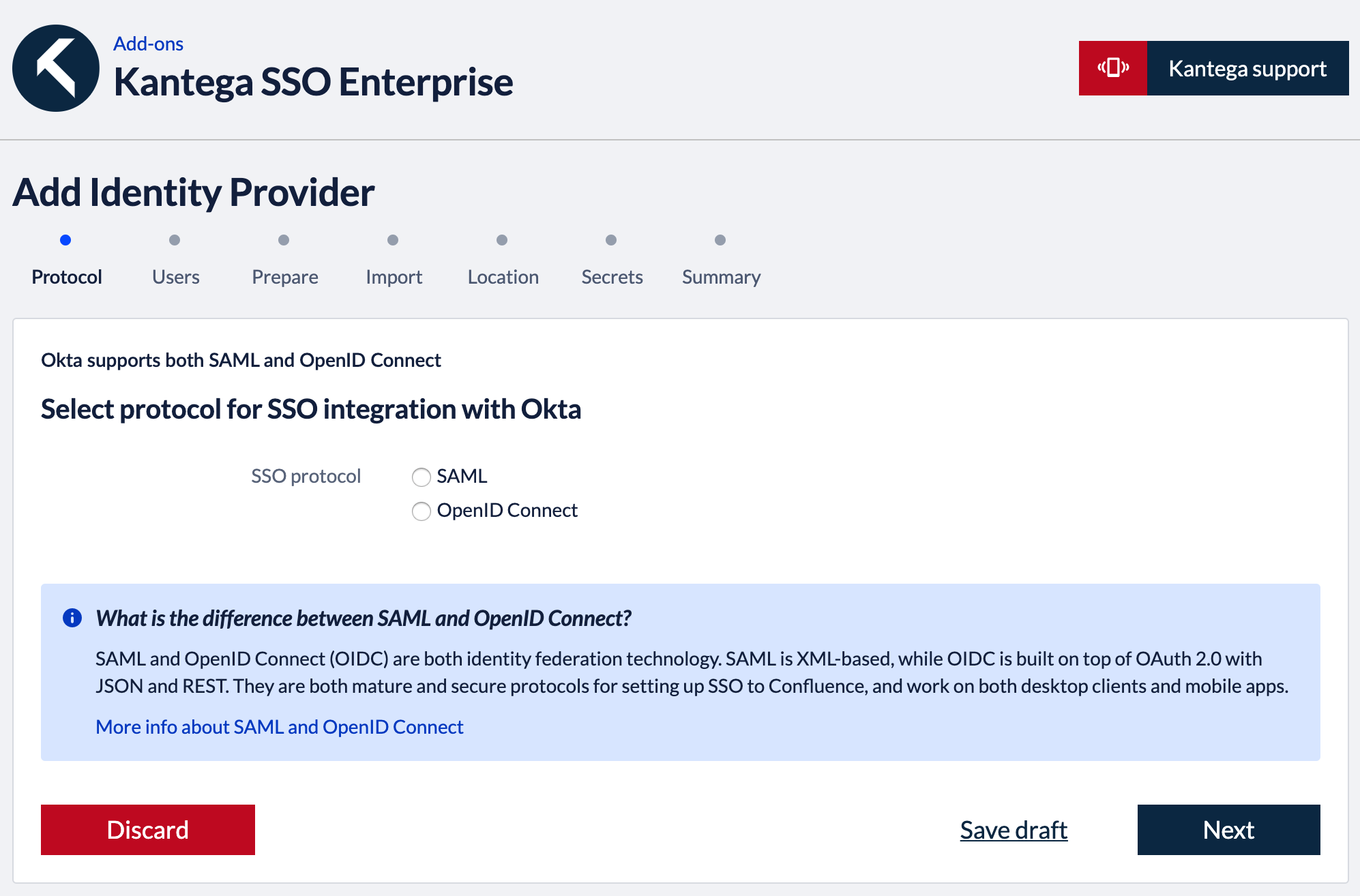
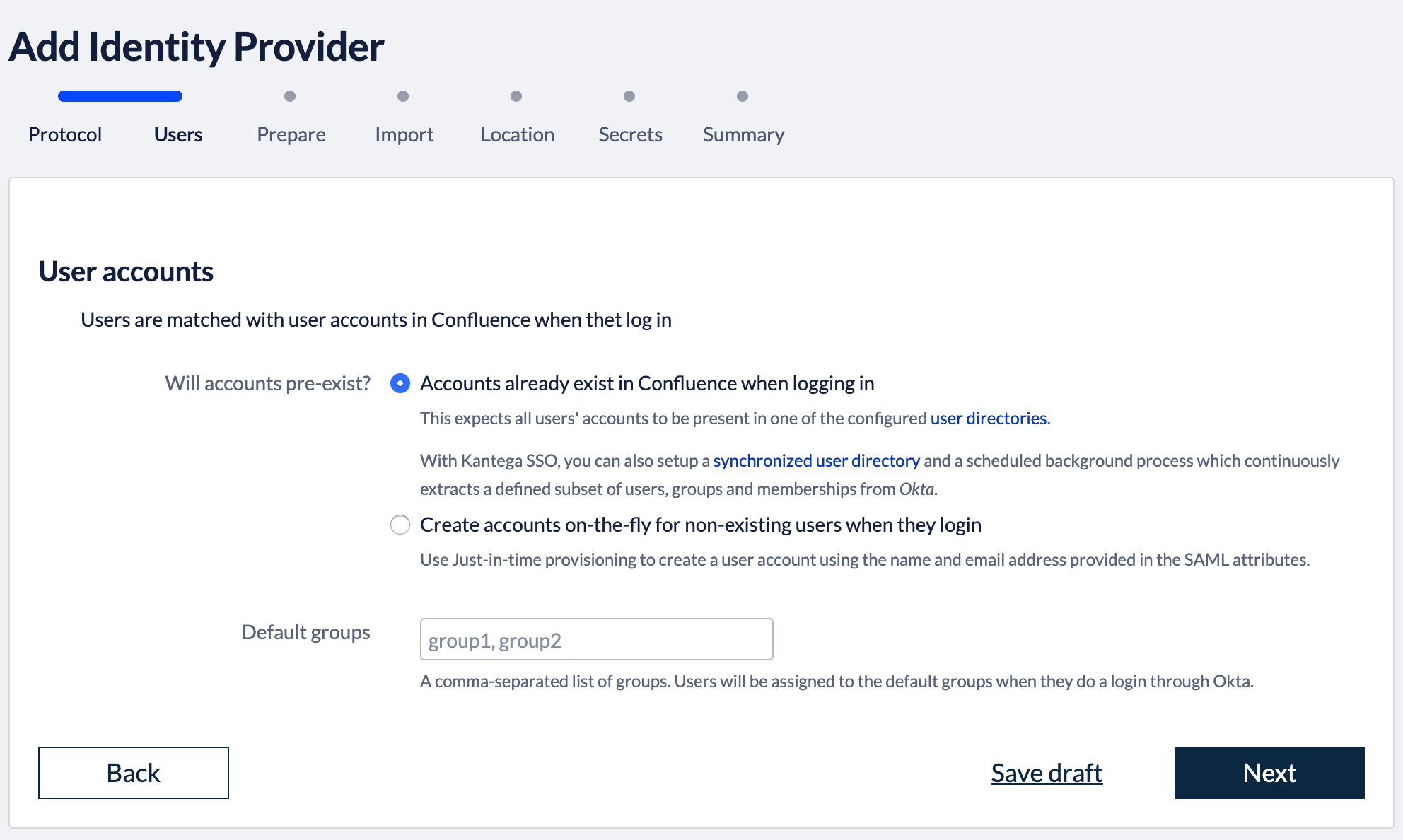
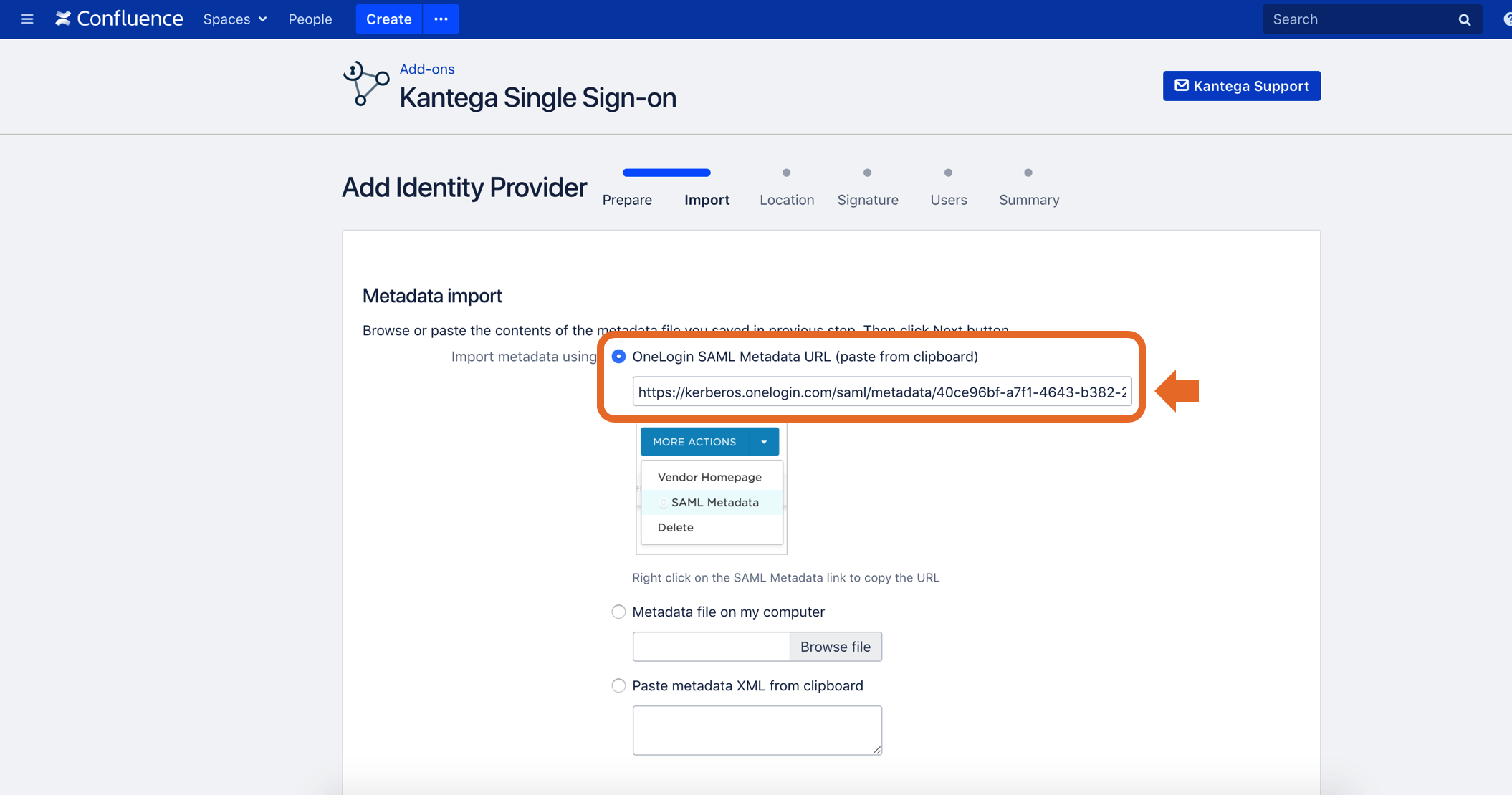
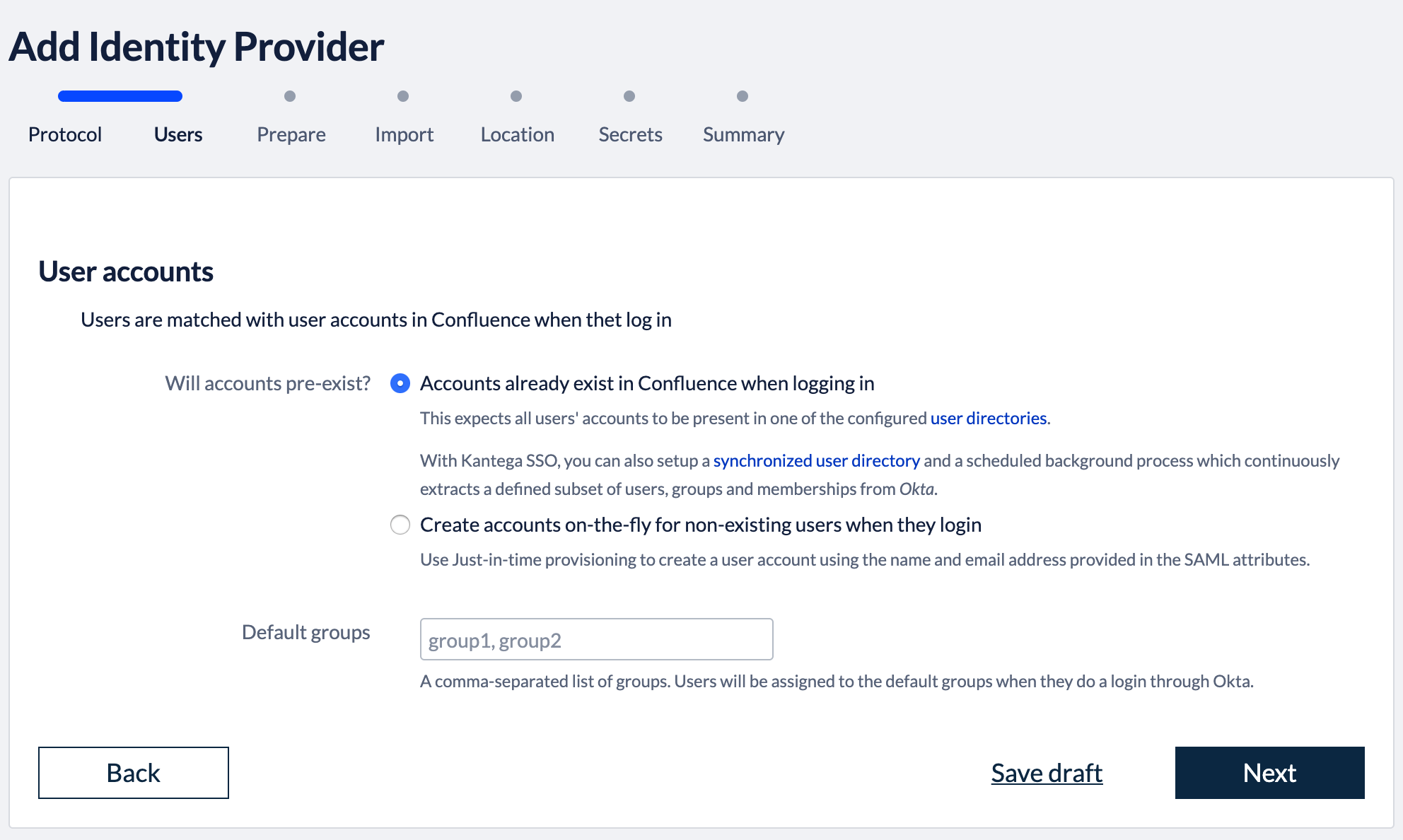
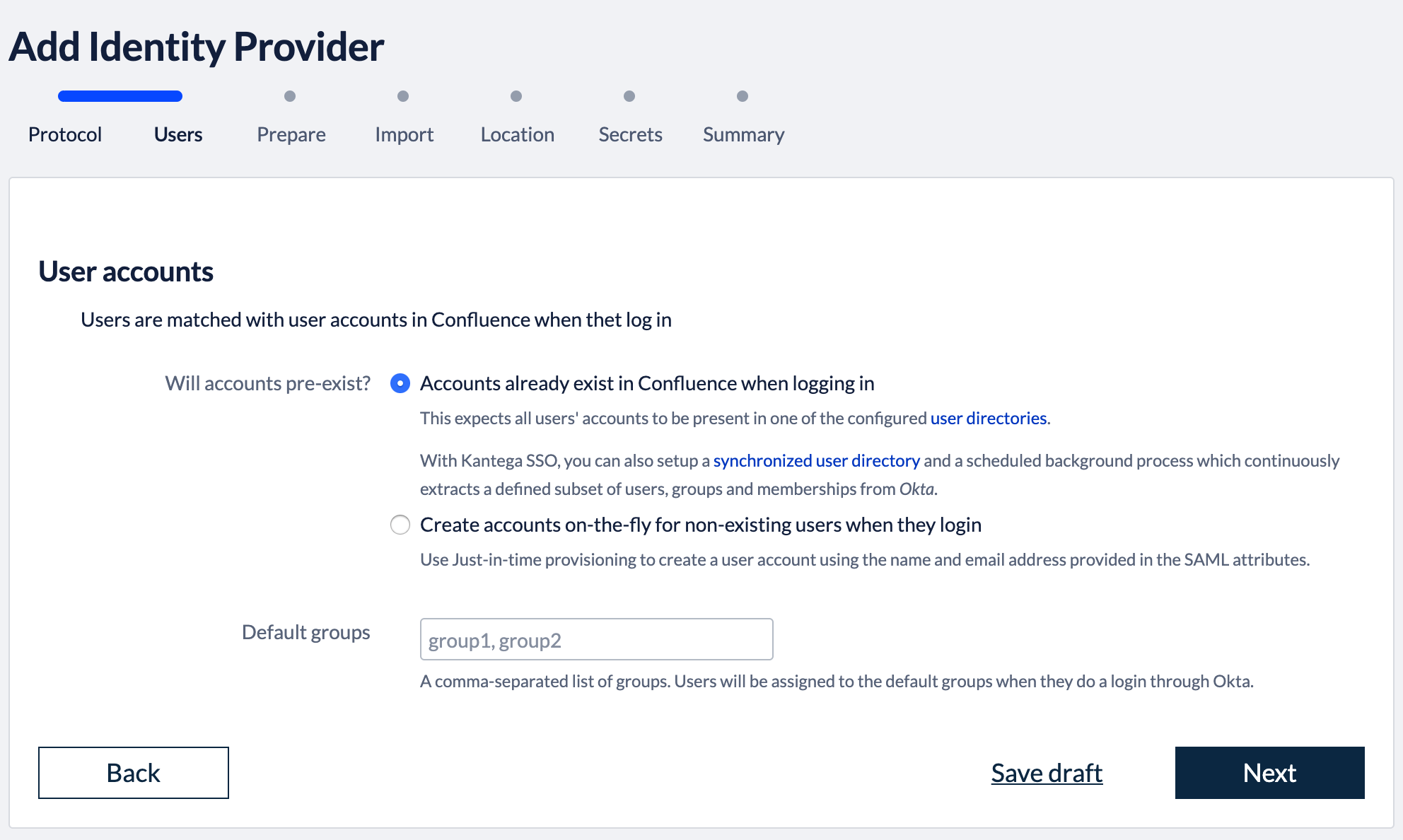
1. Select provisioning method
The Atlassian applications needs to have information about users logging in and their permissions. At this wizard step, we choose whether user and permission data already exist when users log in with SSO or if user records should be created dynamically (just-in-time provisioning).
You can also specify whether users logging in through Onelogin should be added as members to a set of default groups automatically.
Select provisioning method, default groups and click “Next”.
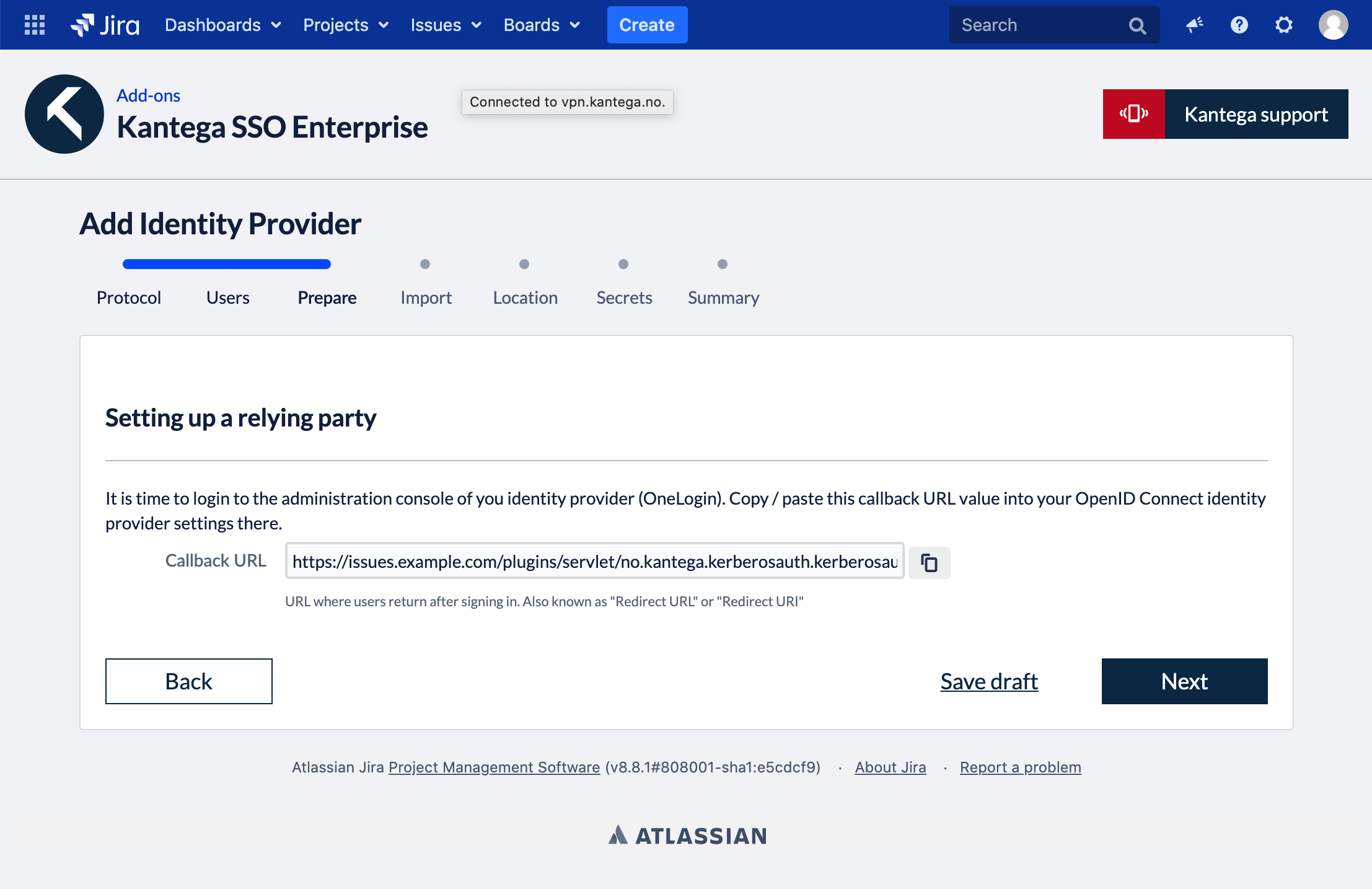
2. Callback URL
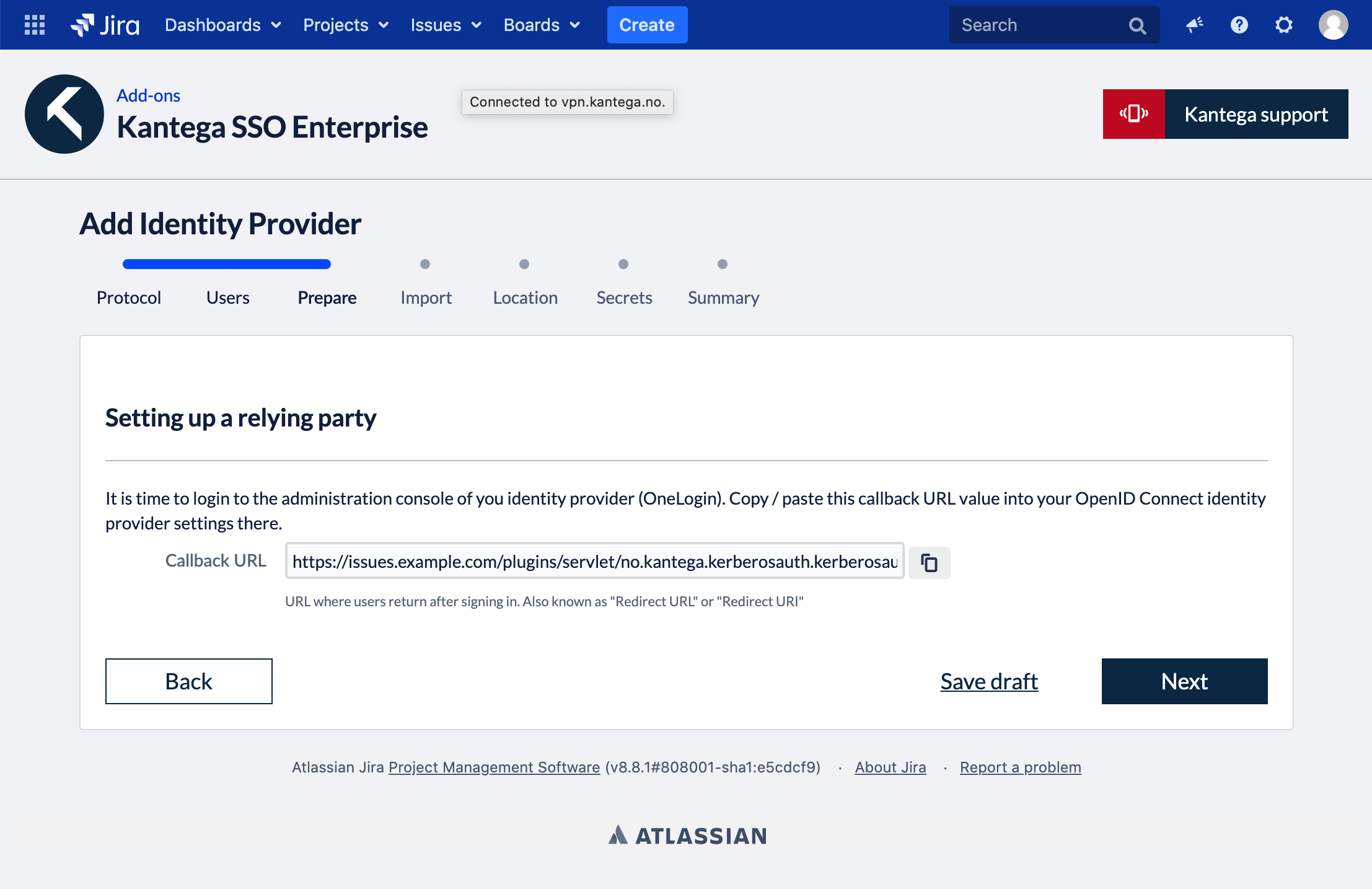
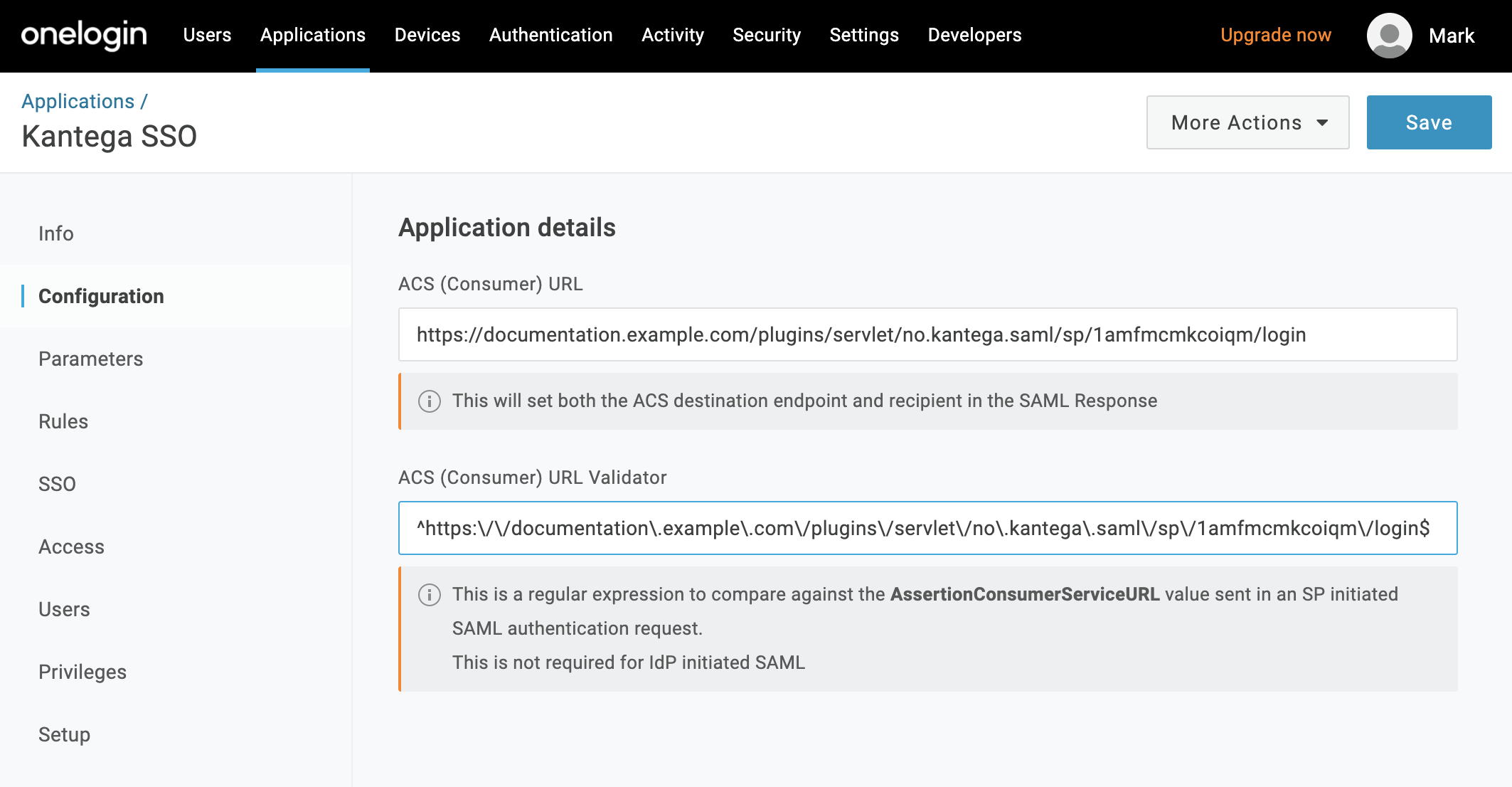
The field “Callback URL” will be needed when configuring your identity provider. Copy this URL value (We will make use of this in the next step)
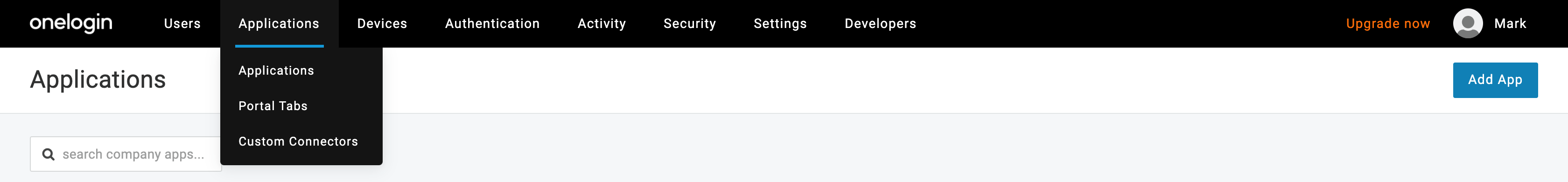
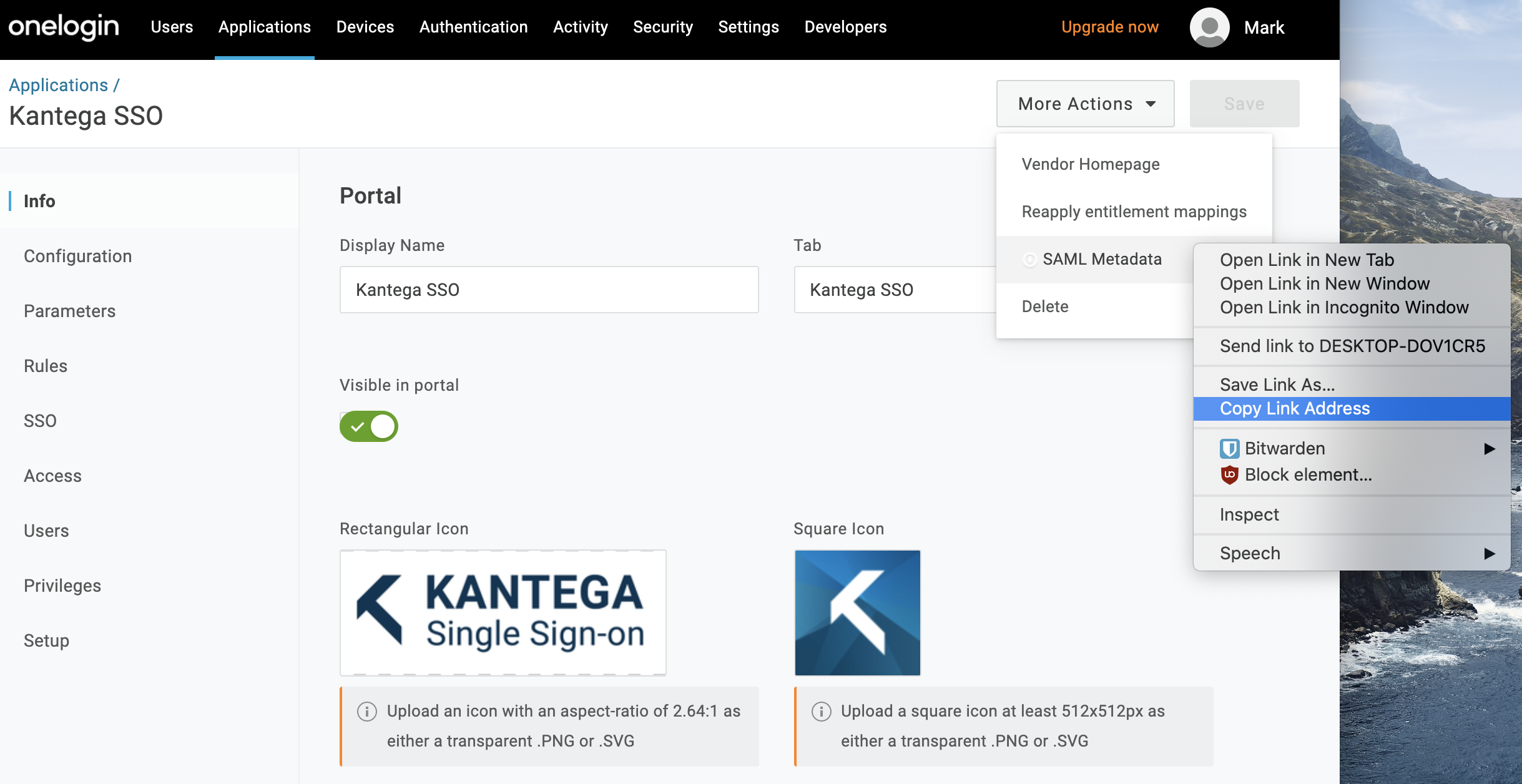
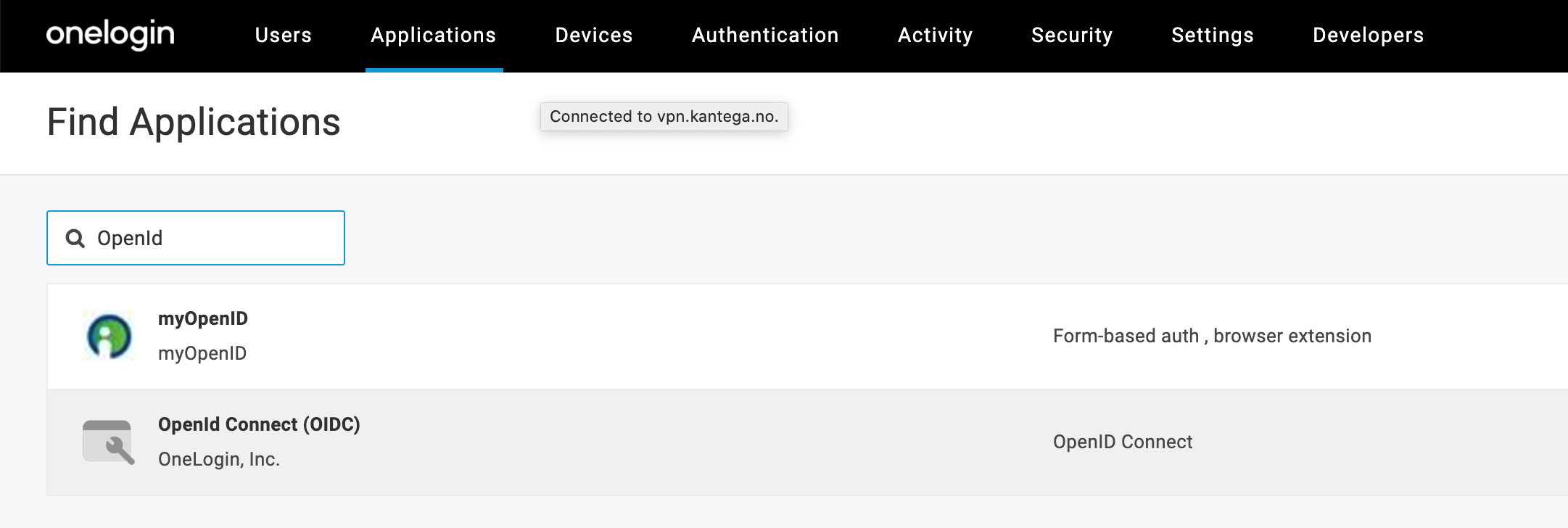
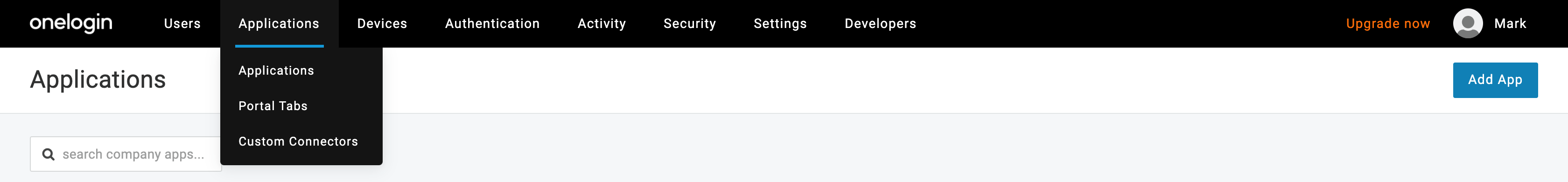
Open your OneLogin Admin Console.
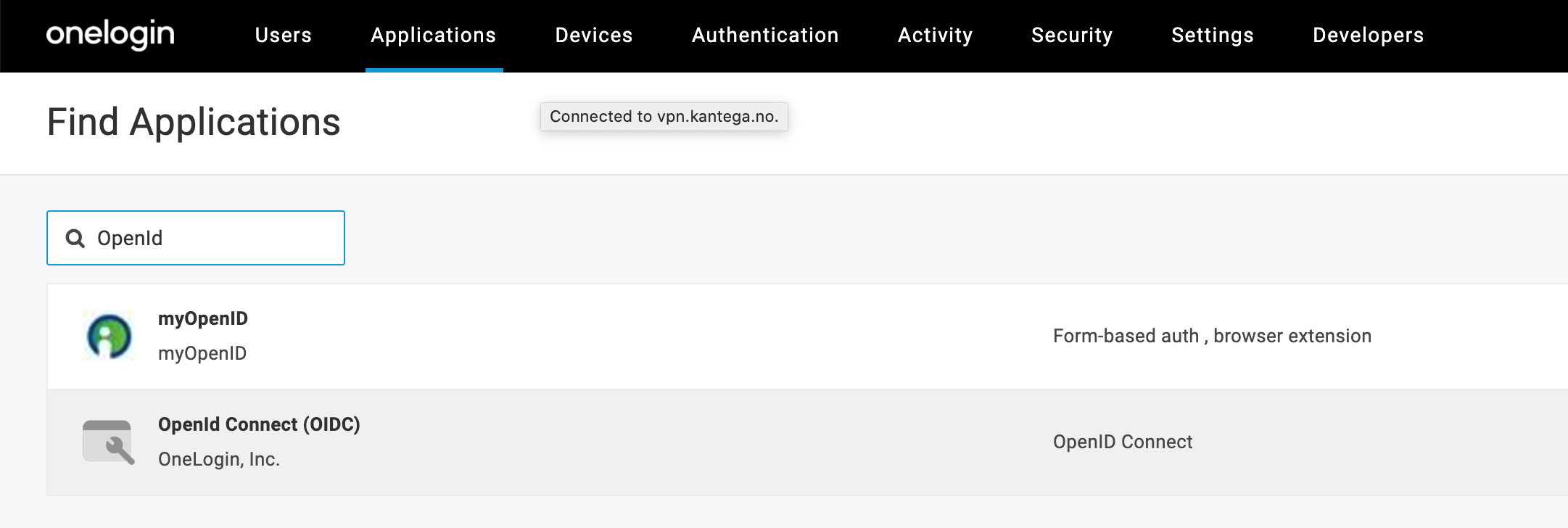
Click the "Applications" tab, then "Add App".
In the search console, find and select "OpenId Connect (OIDC)"
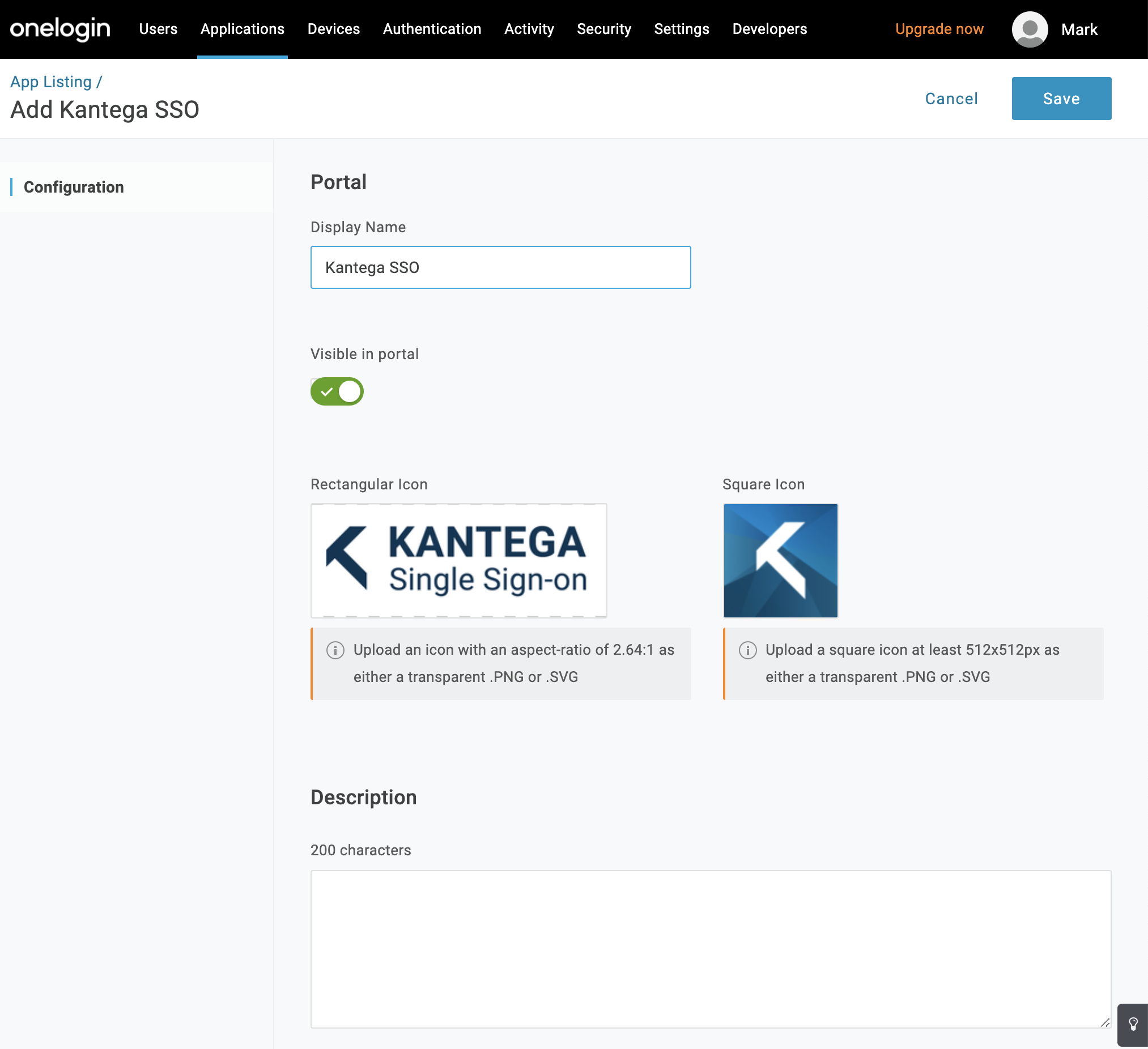
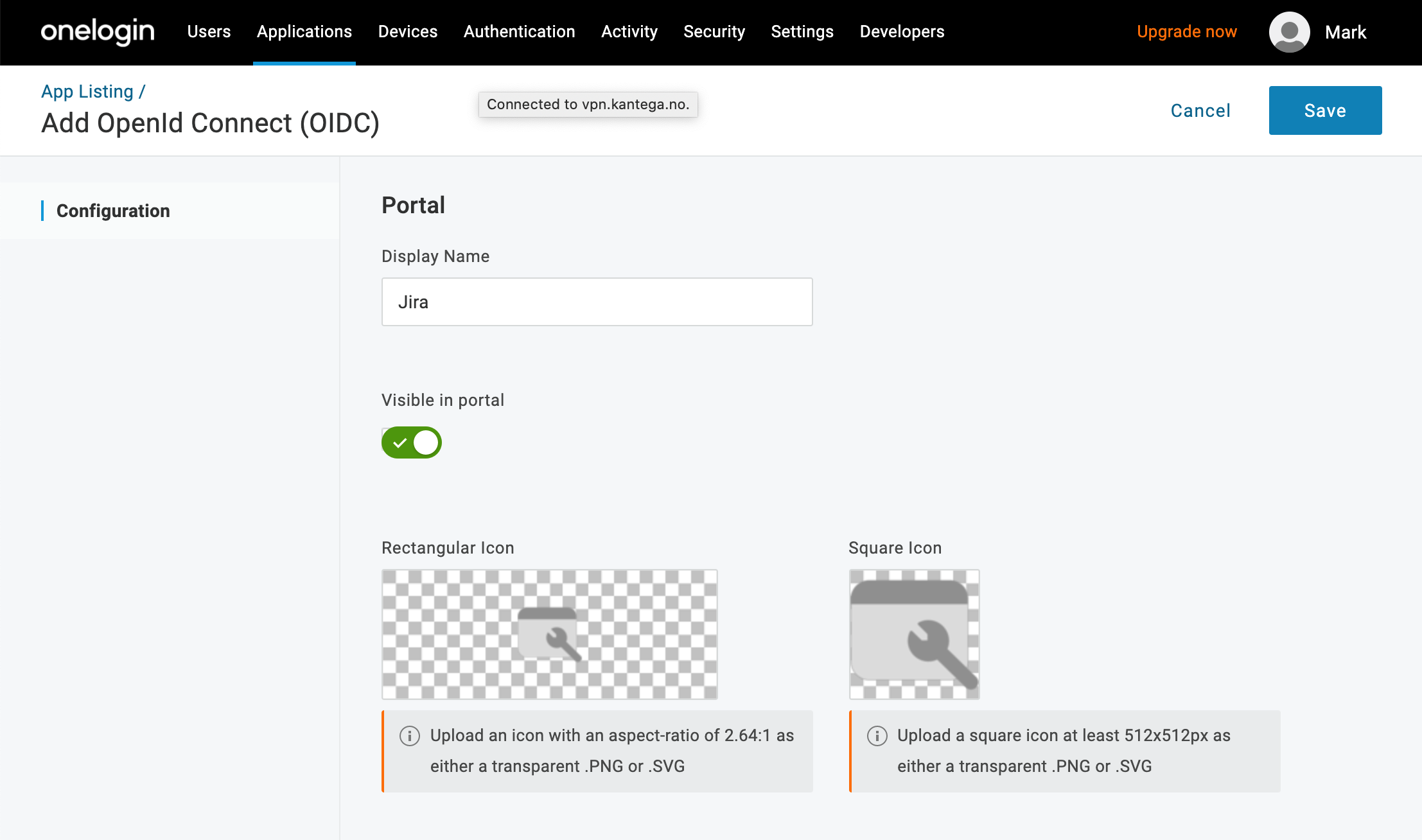
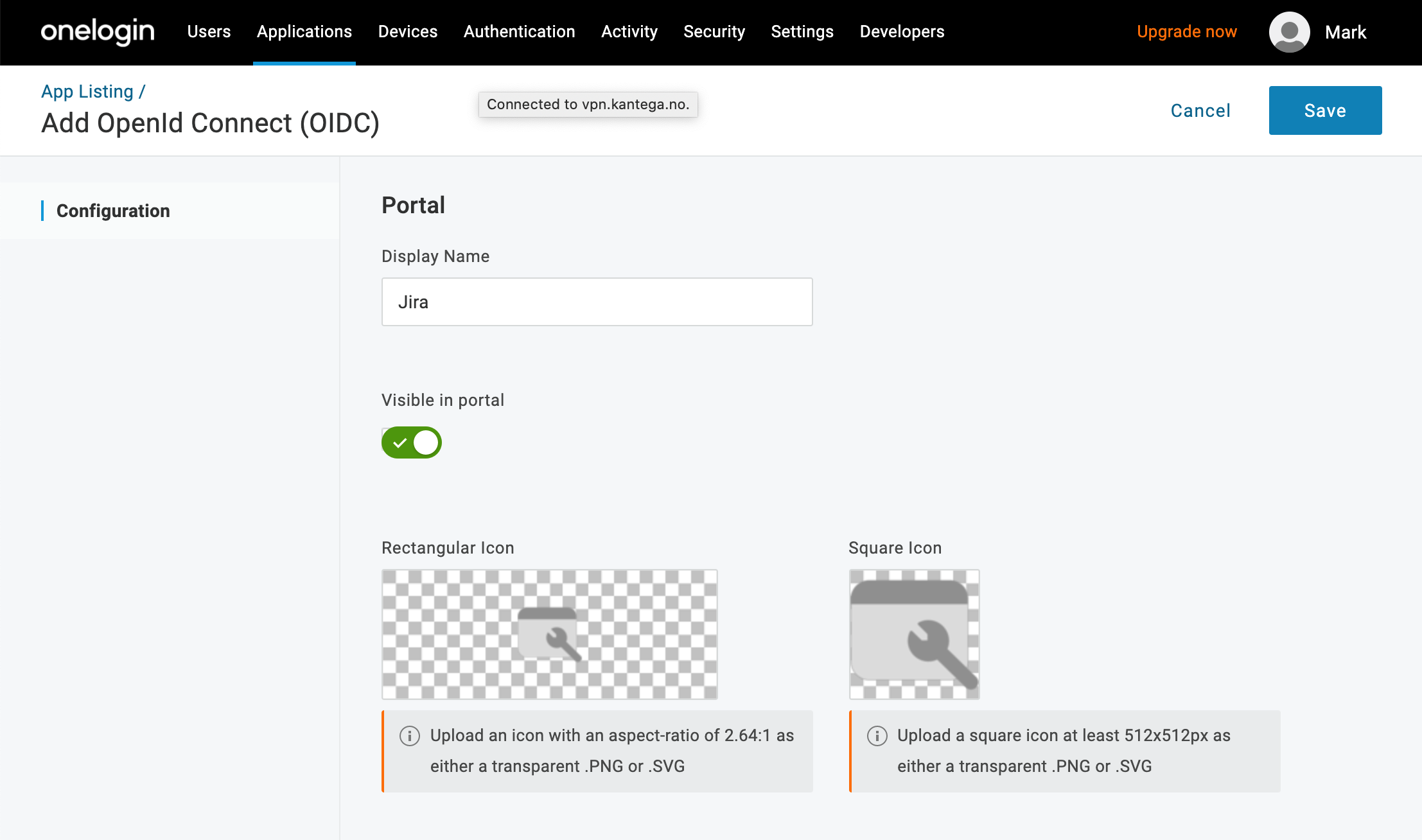
Give the app a Display Name, and click “Save”. Optionally, you can also give the app an icon and a textual description.
Assure the correct roles and users have access to the new application
Under the "Roles" tab you may select what roles should have access to the new application.
You may also give single users access. This is under the specific user found under the “Users” top menu.
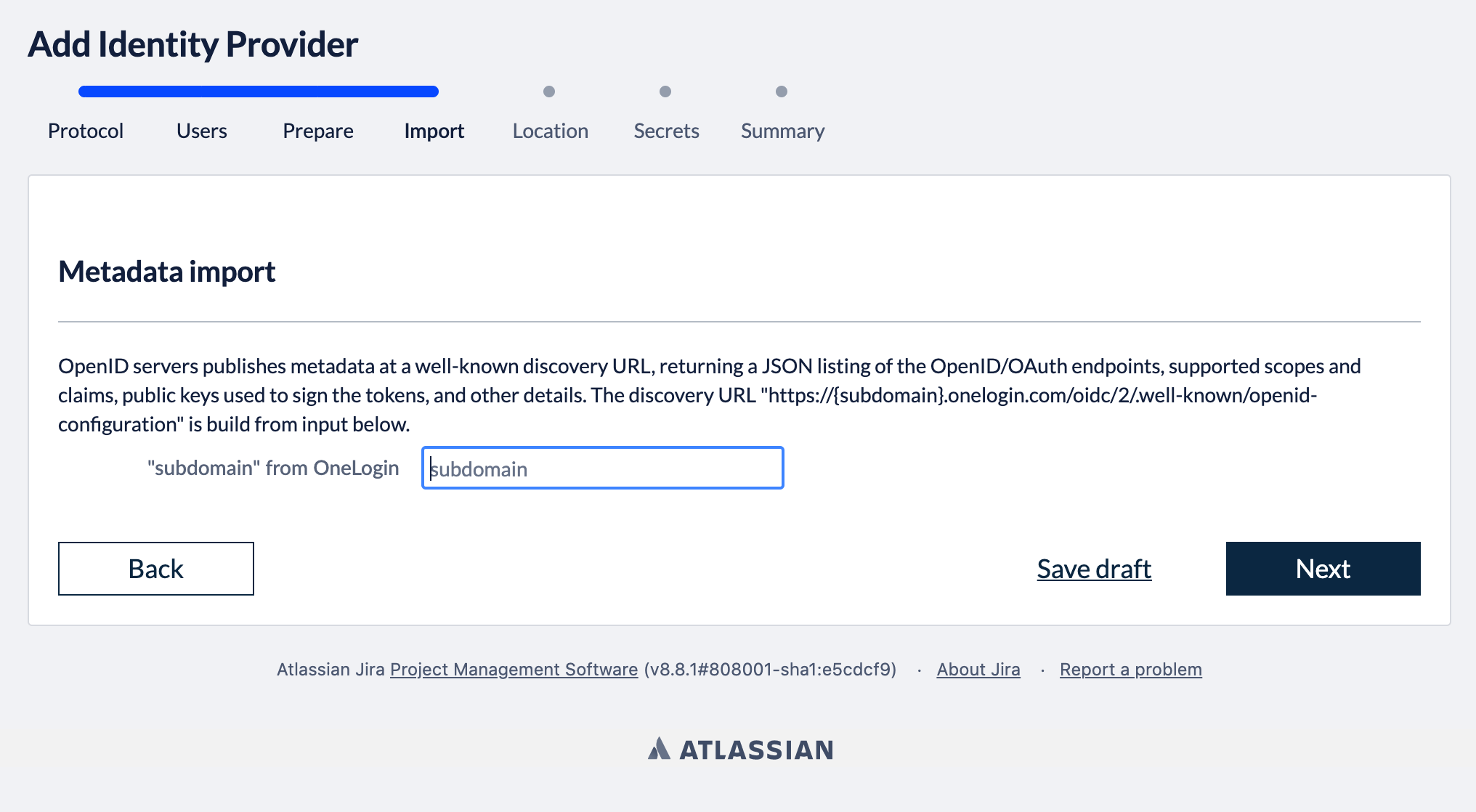
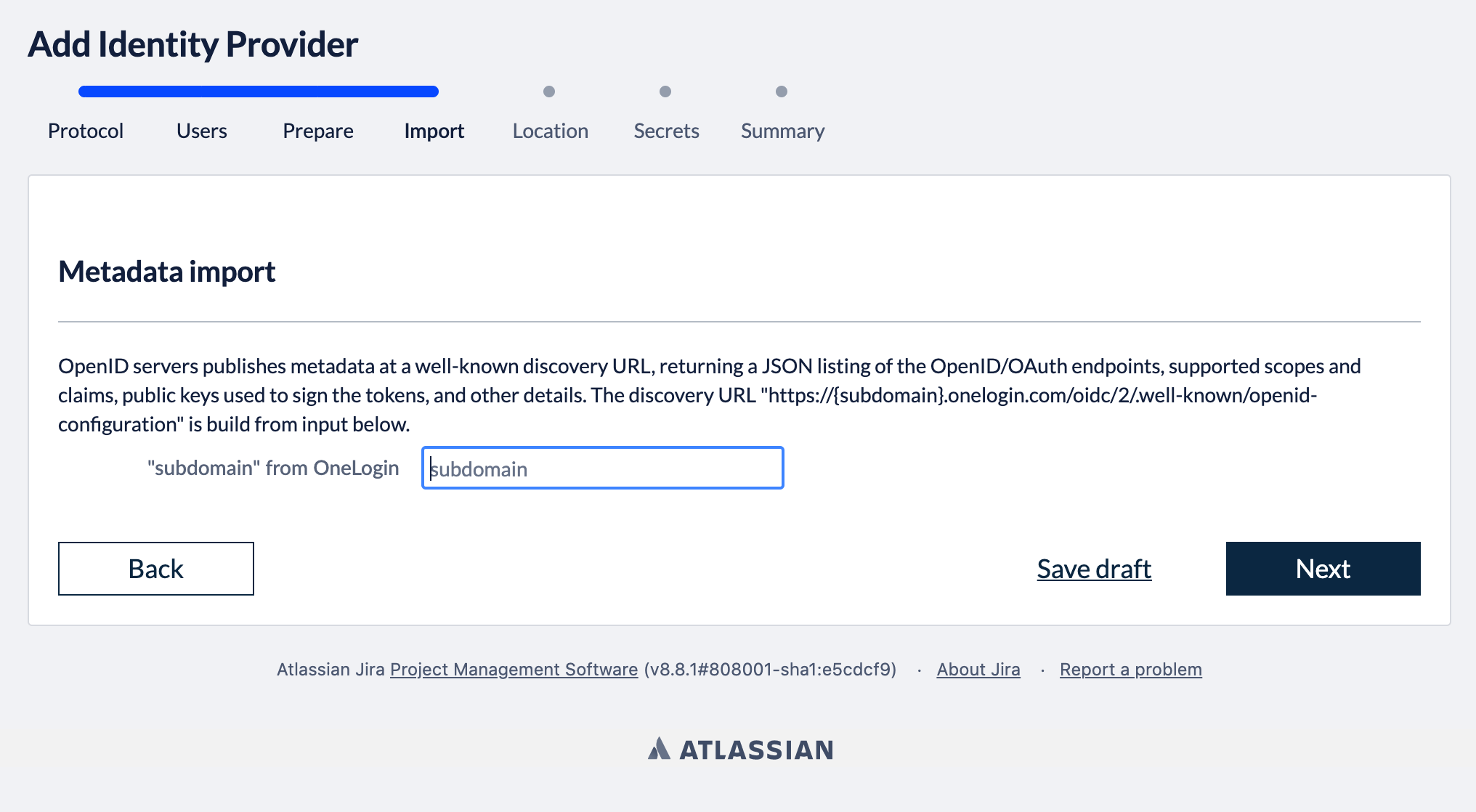
Go to the Kantega SSO wizard and click “Next” in the import step
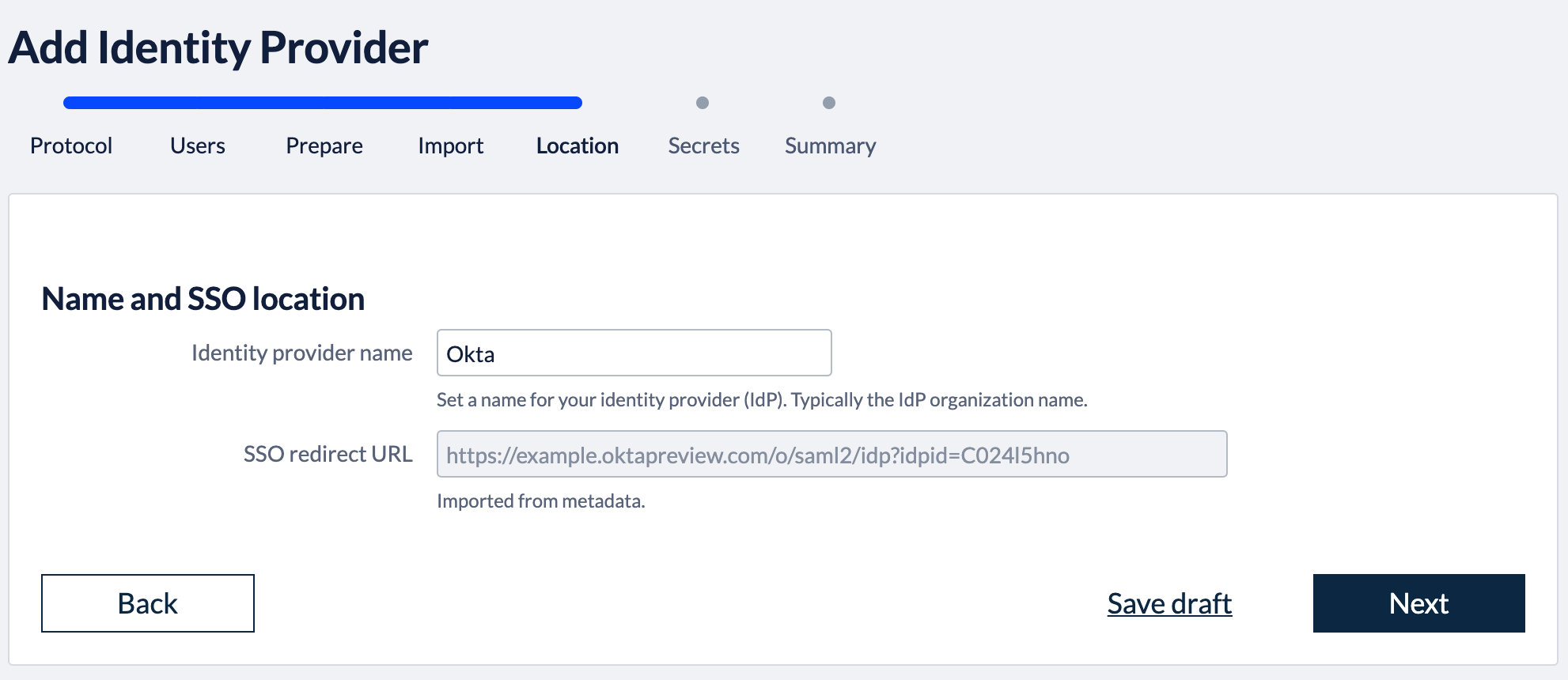
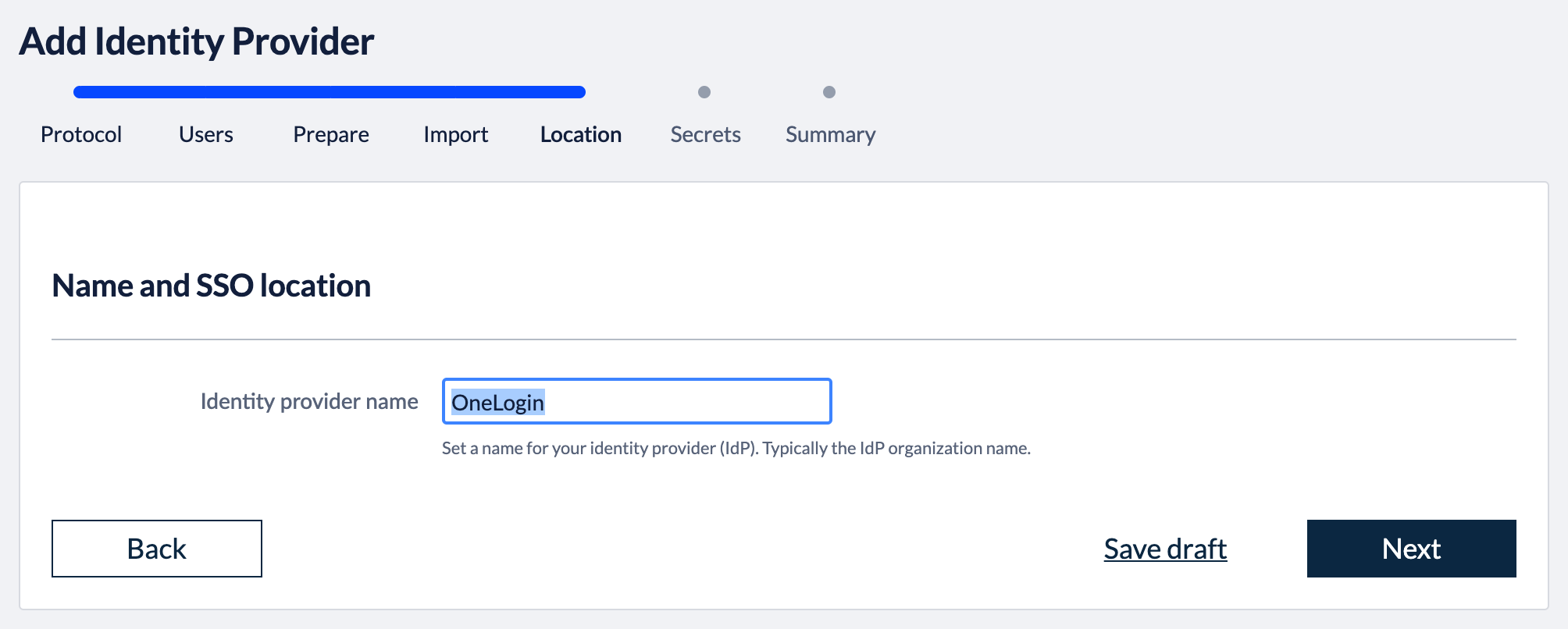
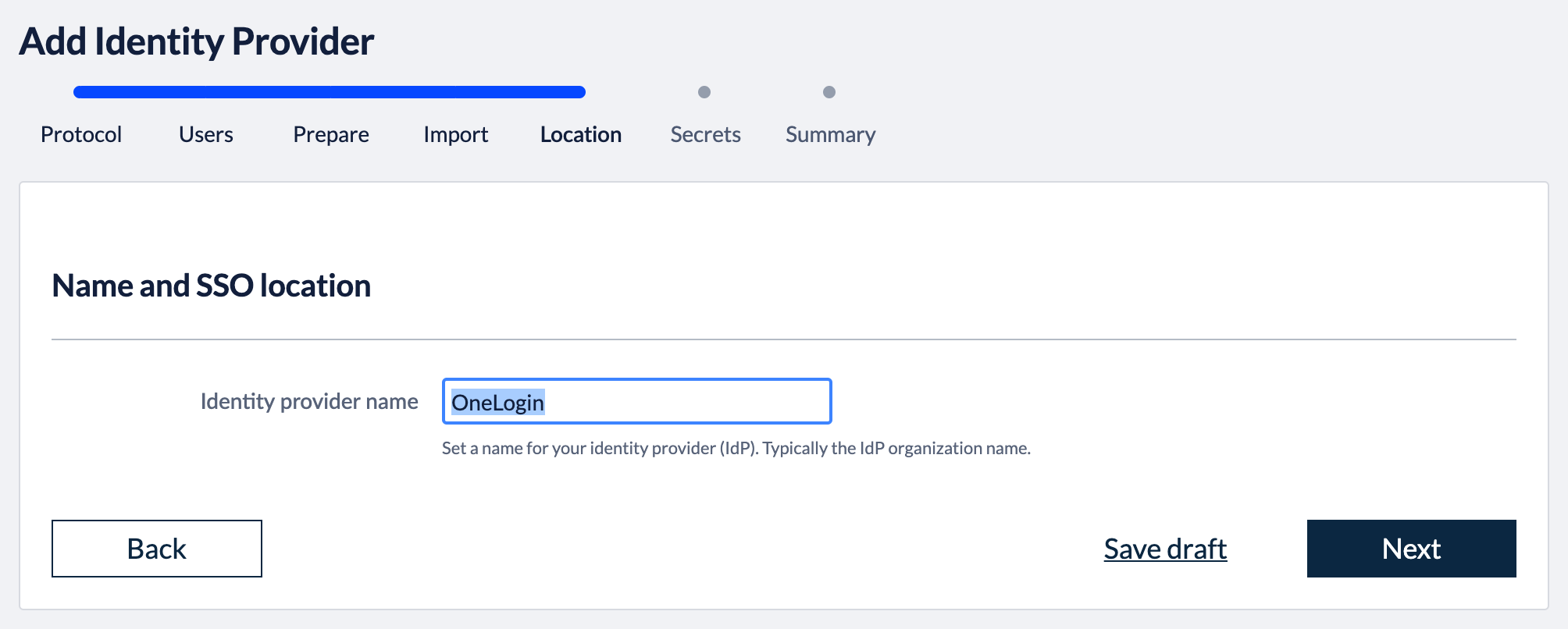
5. Identity provider name
Fill in a name for your configuration, by default this is “Onelogin”. Click “Next”
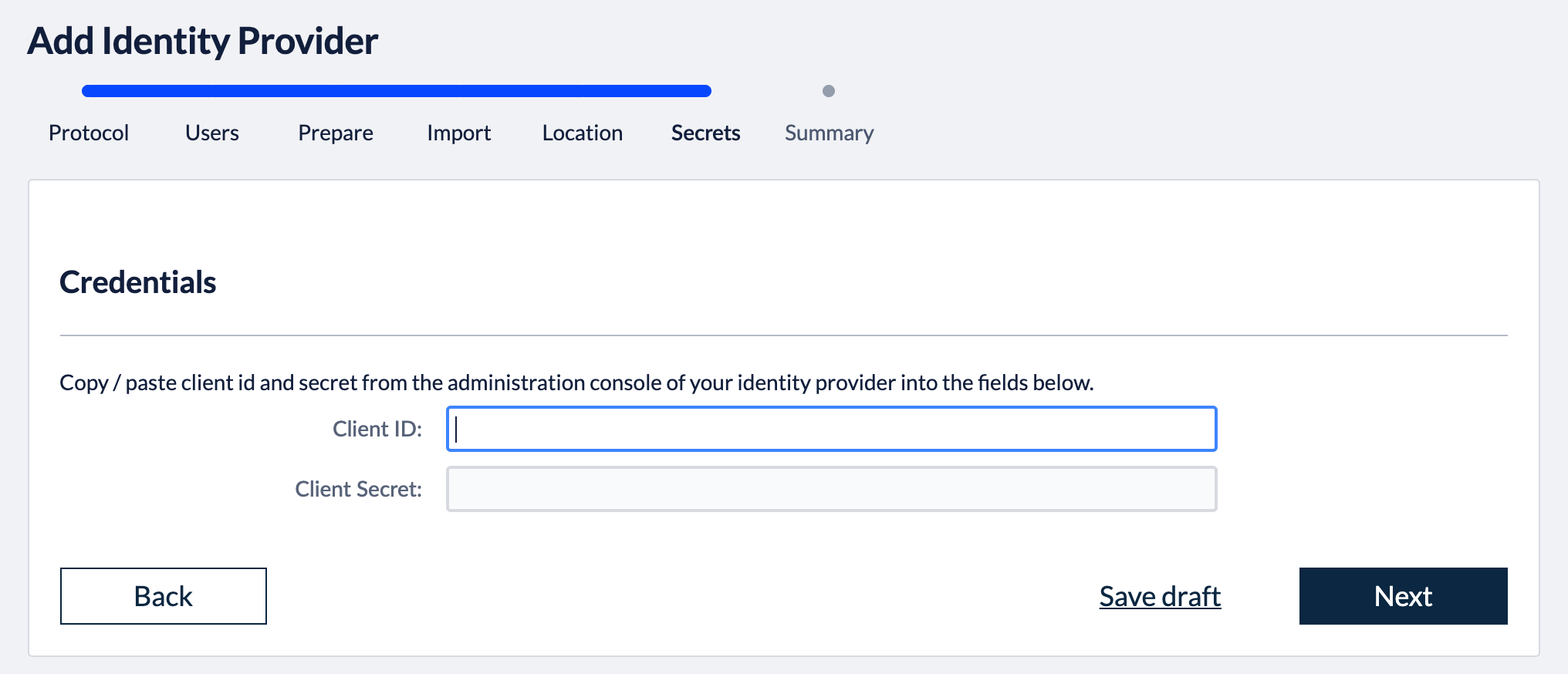
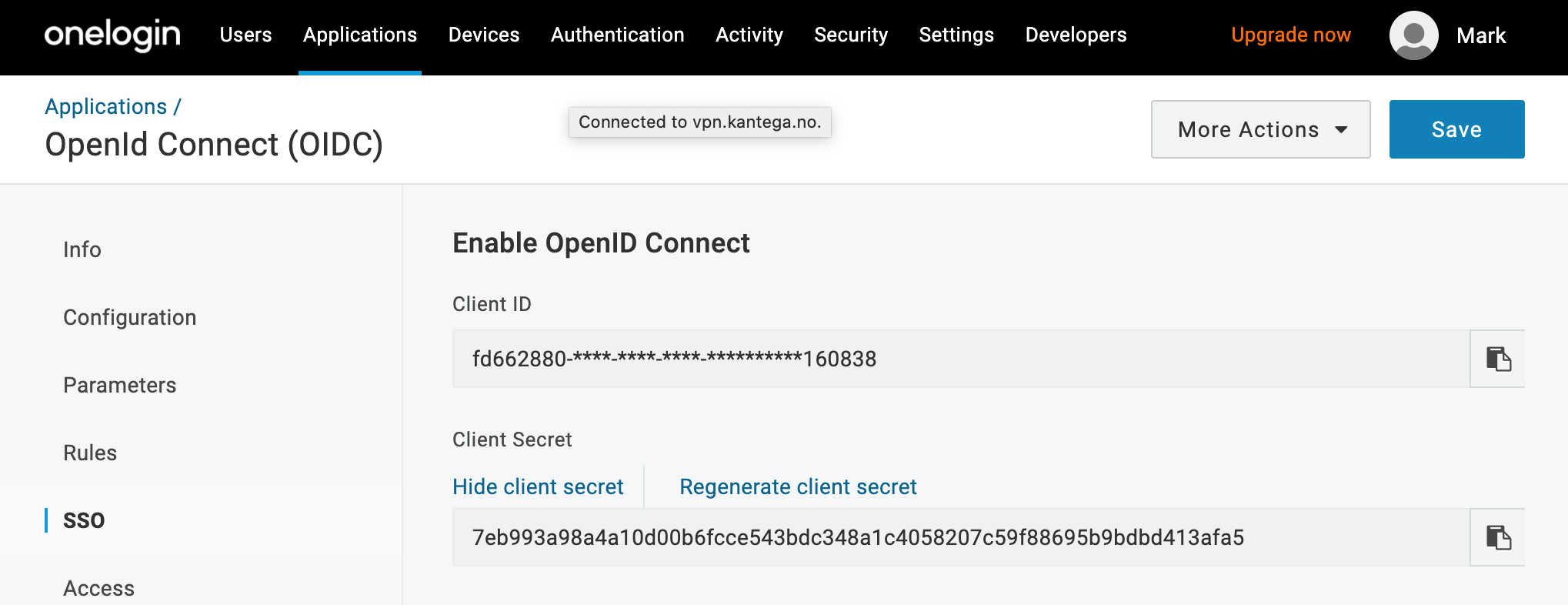
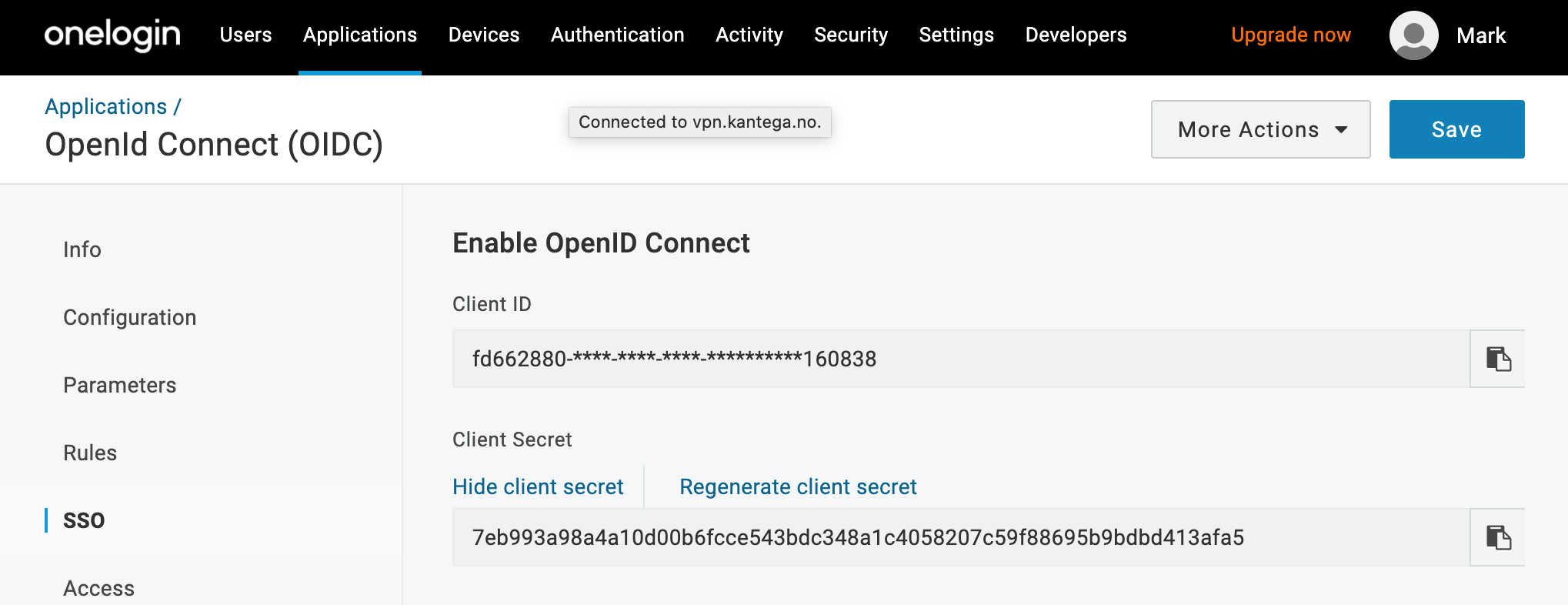
6. Client id and secret
In this step, we will insert client credentials from Onelogin.
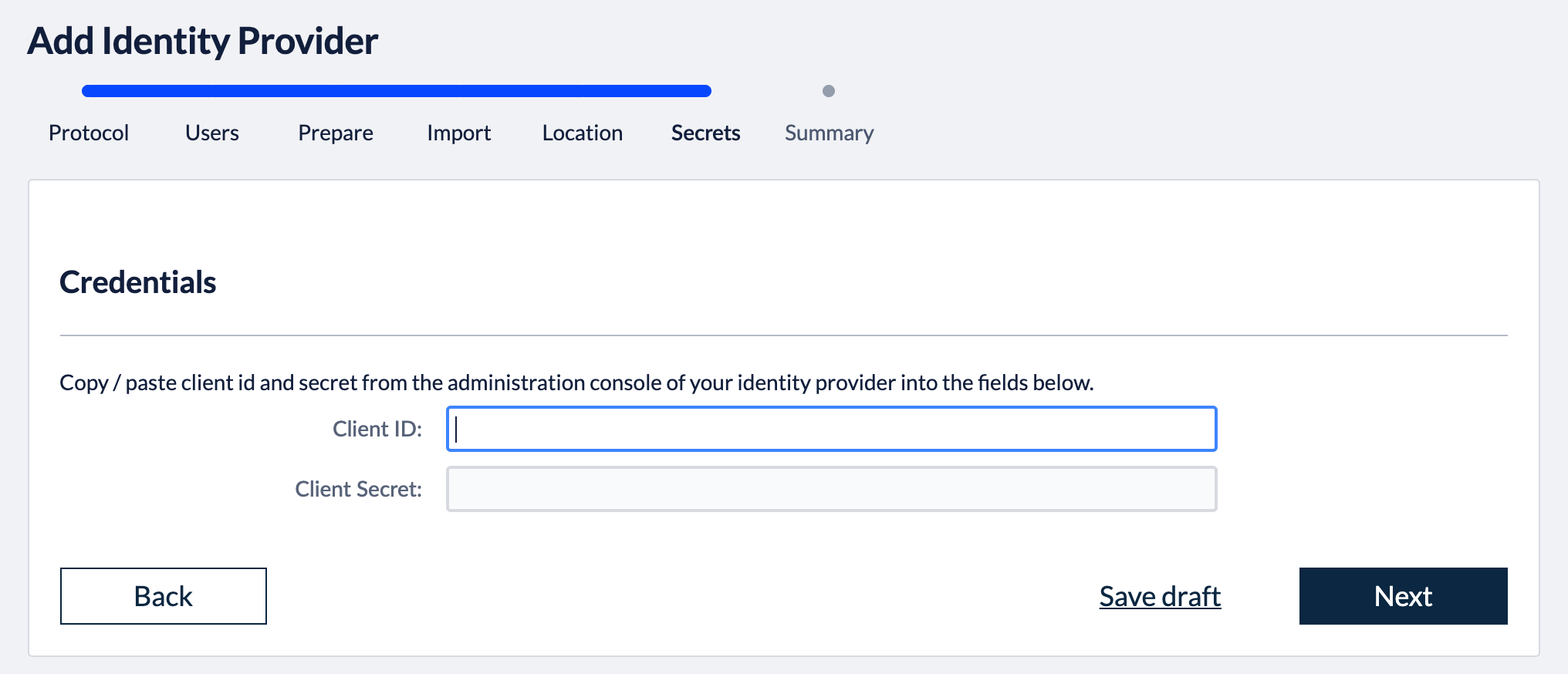
These two values are found in the SSO settings in Onelogin:
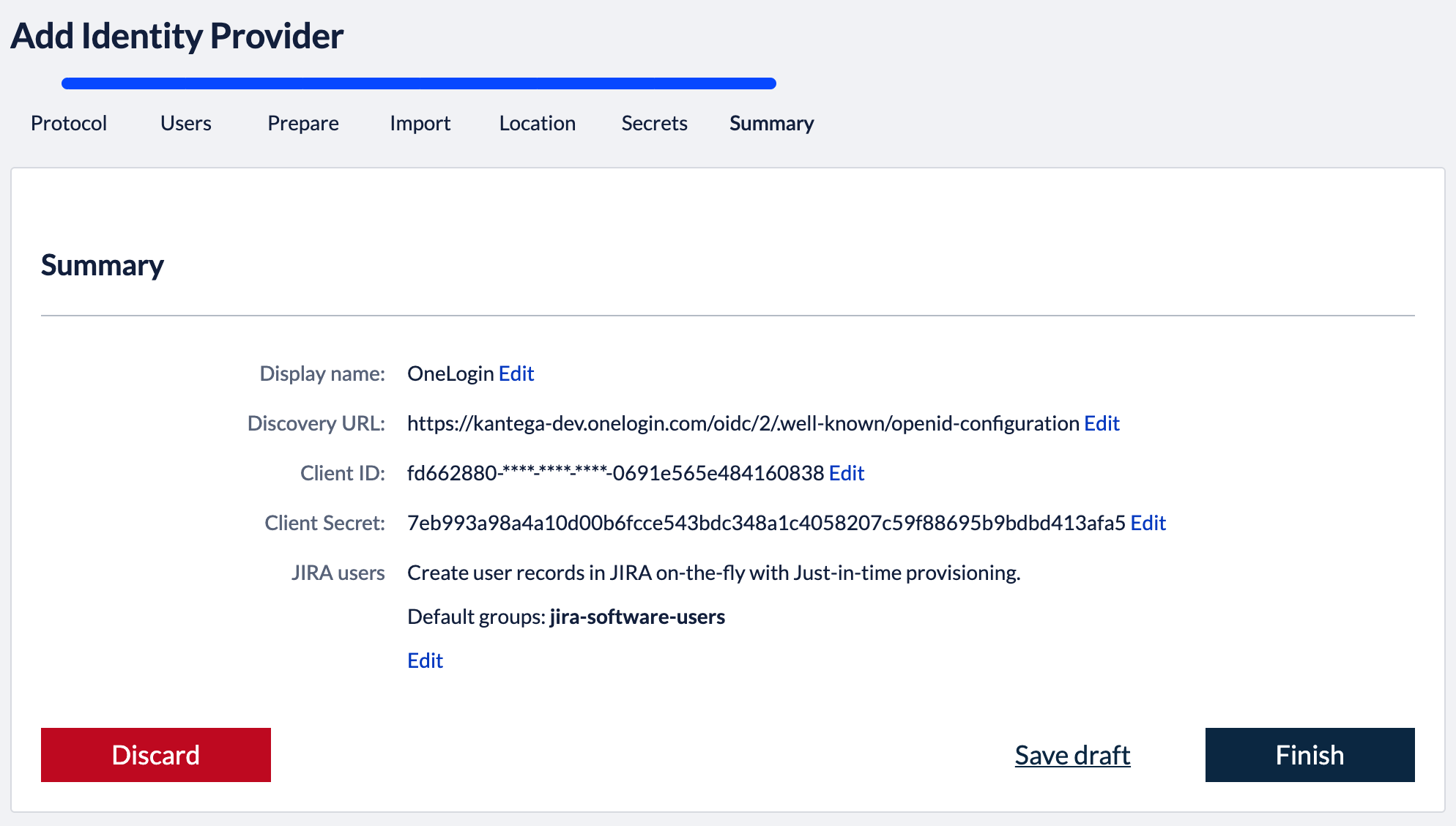
Click “Next”, and you will see a summary page of your Kantega SSO setup.
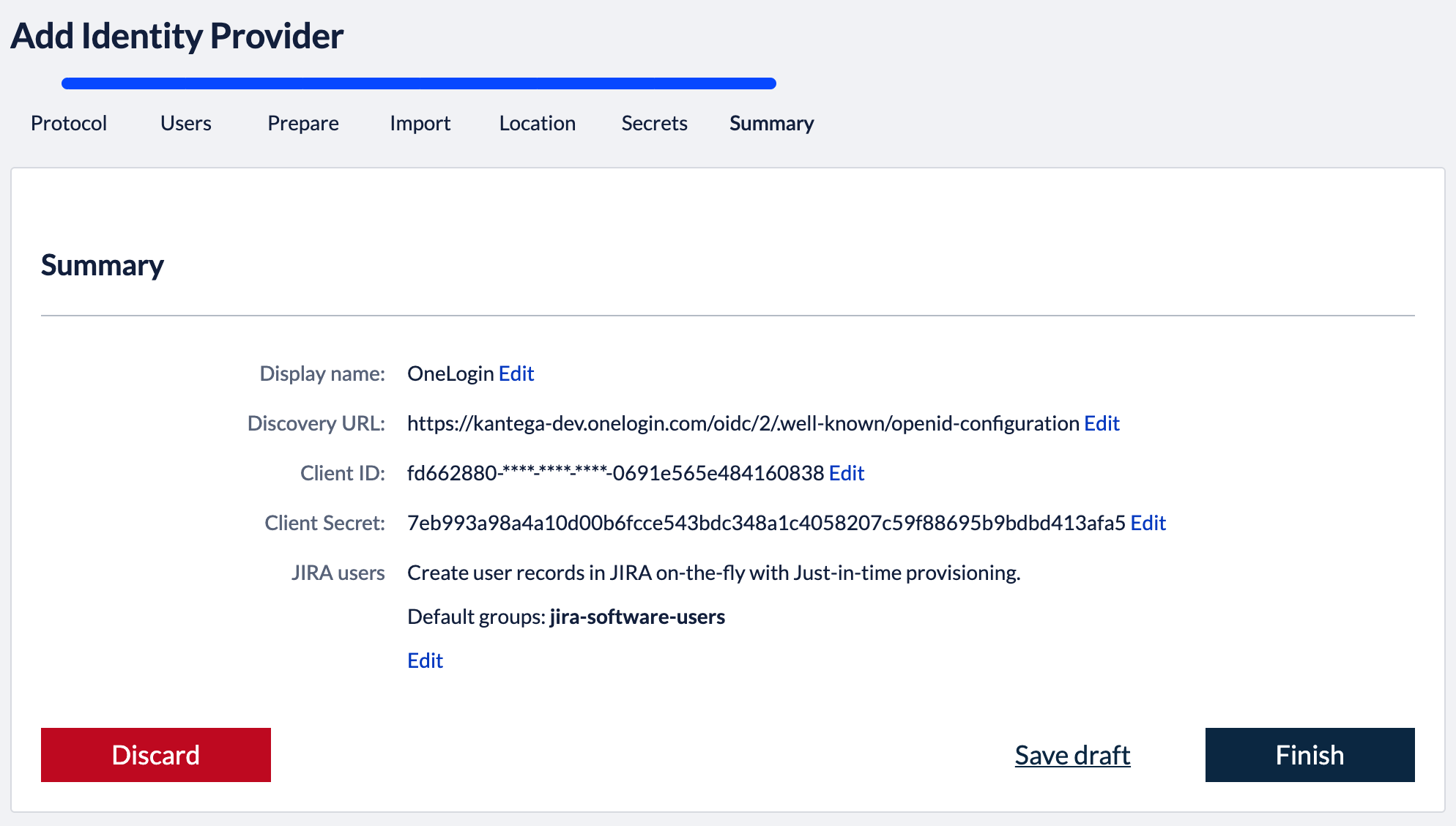
7. Summary
Validate your setup and click “Finish”.
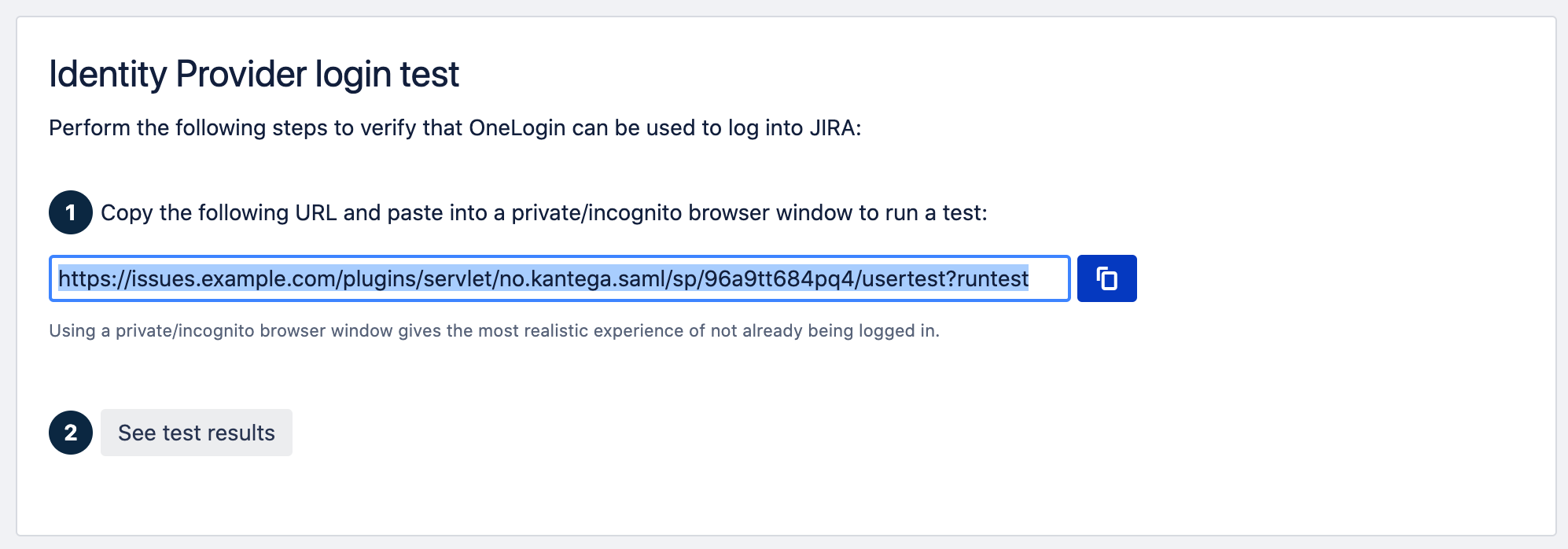
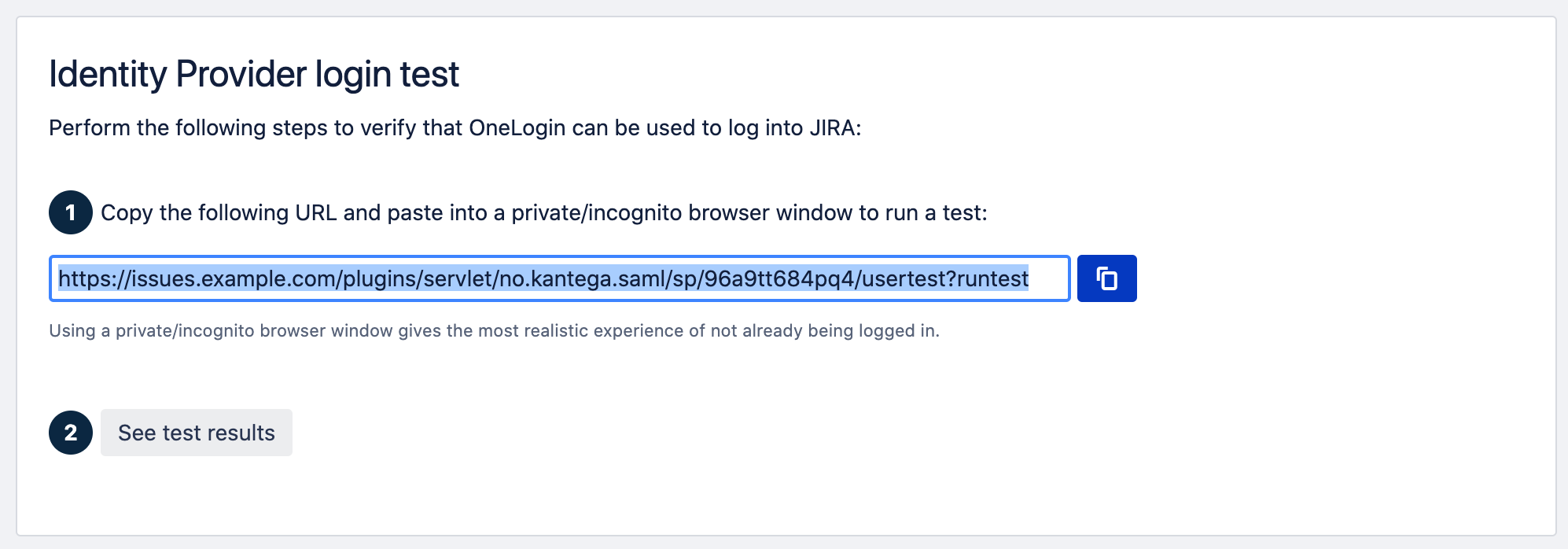
8. Test and verify setup
On the next page you will be given a link to perform a test of your setup.
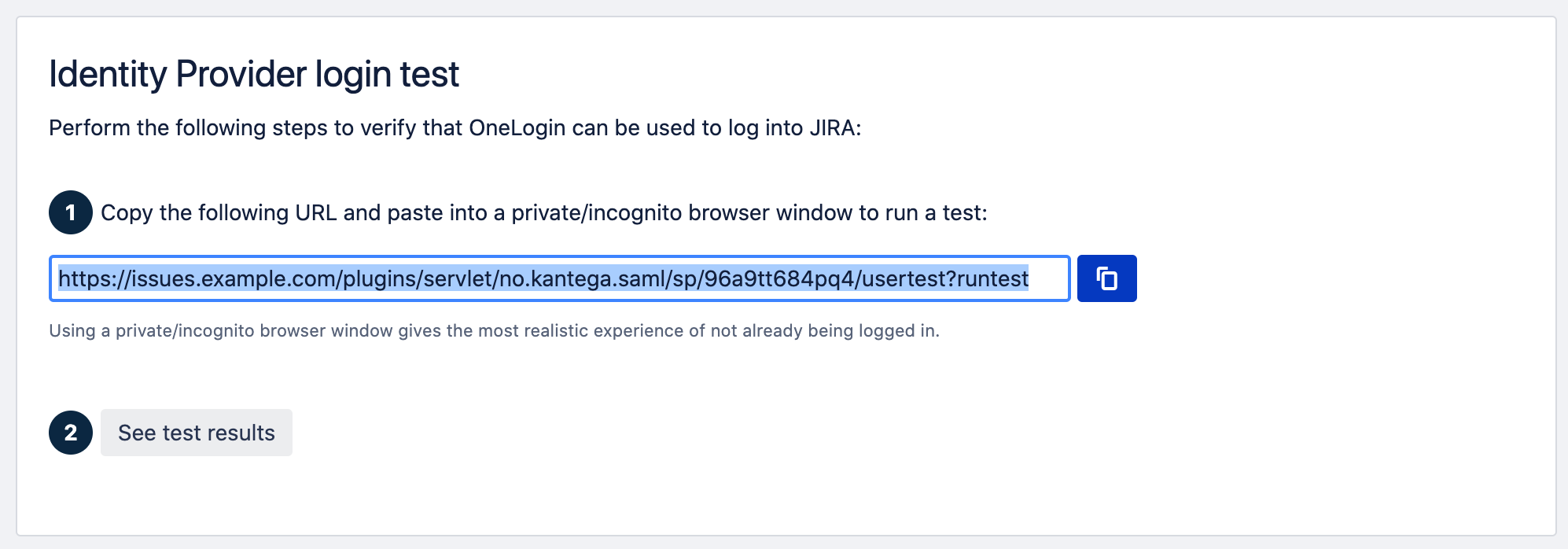
The test verifies that users are allowed to authenticate with the current configuration, and you get feedback on whether the current user is found in Atlassian application. You are also able to fix user lookup issues (selecting the right username attribute and express username transformation rules) and select data attributes for just-in-time provisioning here. More info about testing av verifying identity provider configurations.
6. Redirection mode
By default, Kantega SSO Enterprise will forward all users to the configured identity provider. However, you can configure both a subset of users who should be login through this identity provider and how they are redirected. More about configuration redirection rules.
.gif?version=1&modificationDate=1587464092509&cacheVersion=1&api=v2)