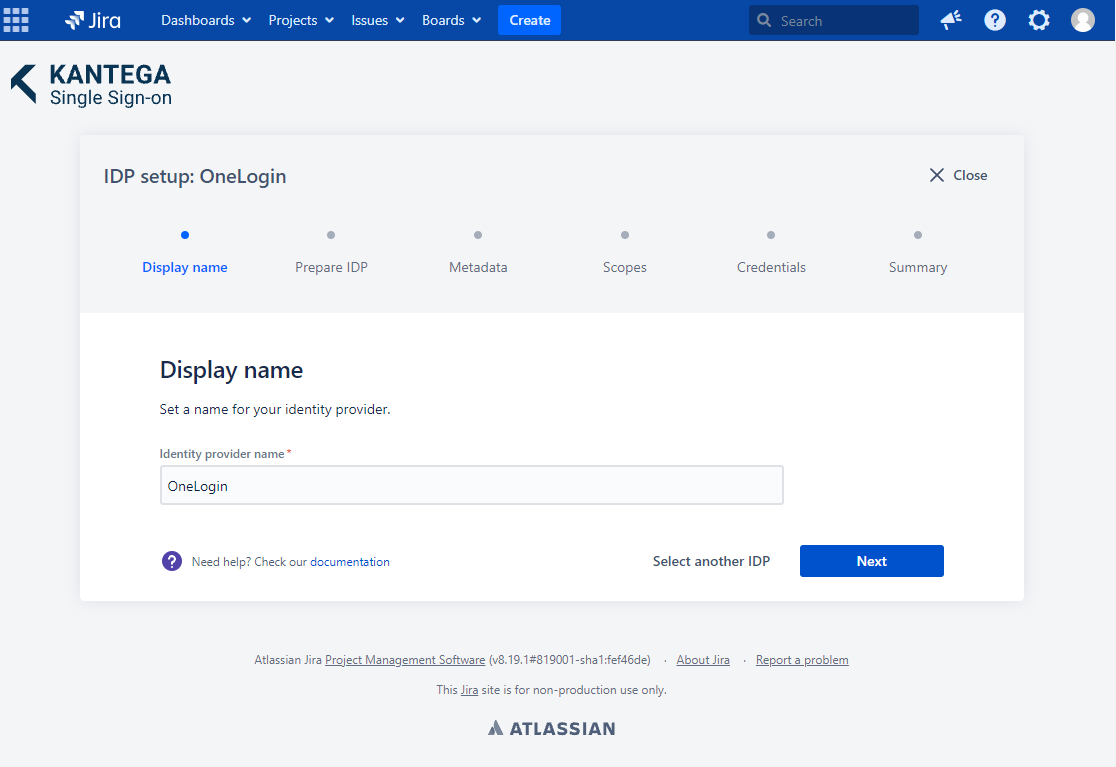
Choose a name for your identity provider. This is the user-facing name, so choose a name your users will recognize. This value can be changed later.
In this step, we will configure OneLogin to work with Kantega SSO. For this, you will need to copy the Callback URL provided. We will use this when setting up OneLogin.
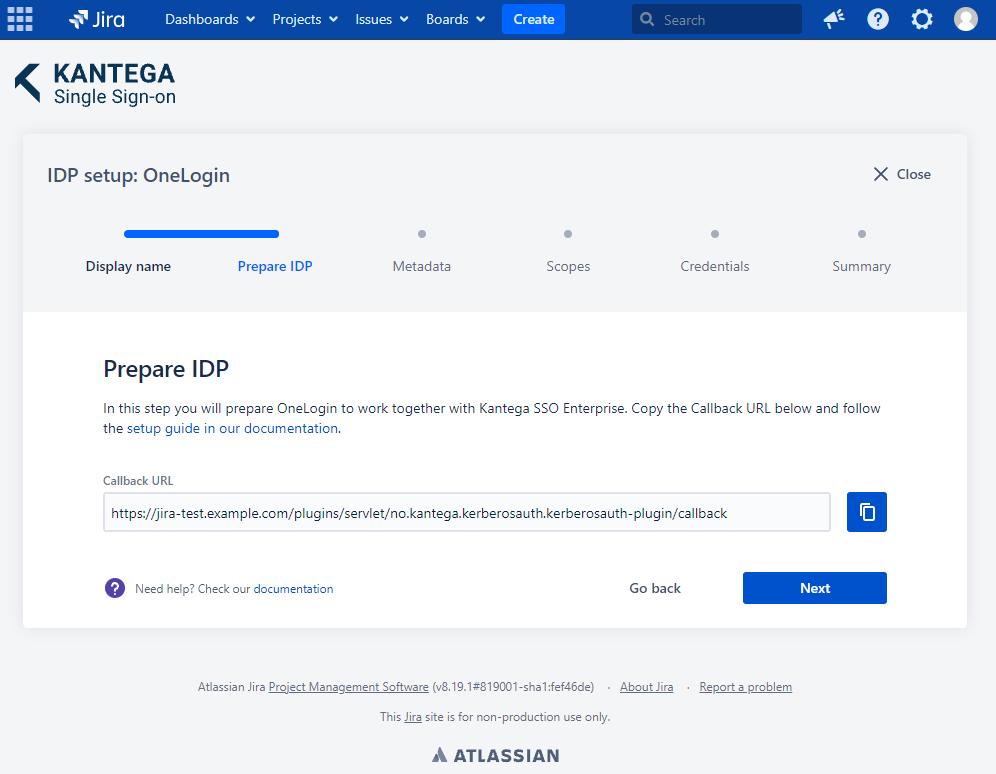
If you are using SCIM with your provider, make sure to check out the documentation for configuring this before proceeding. It might be that you need to configure this first or at the same time as setting up OIDC. |
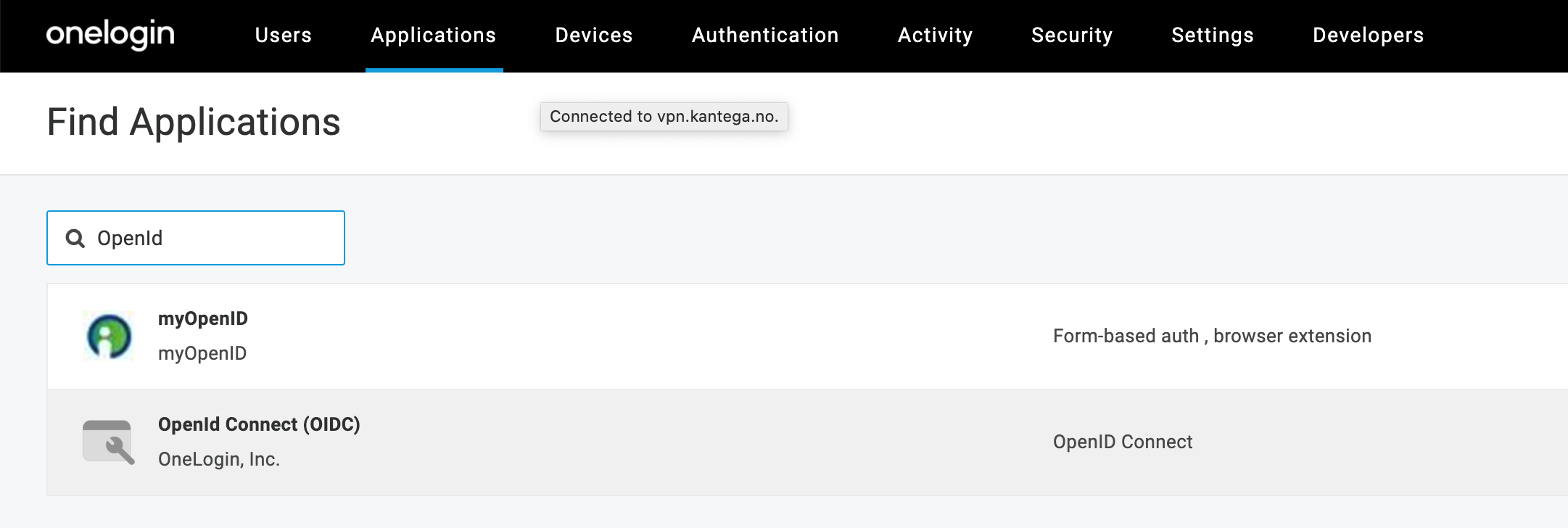
Open your OneLogin Admin Console.
Click the Applications tab, then Add App.
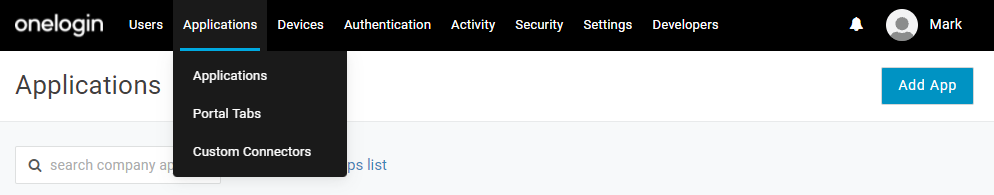
In the search console, find and select OpenId Connect (OIDC)
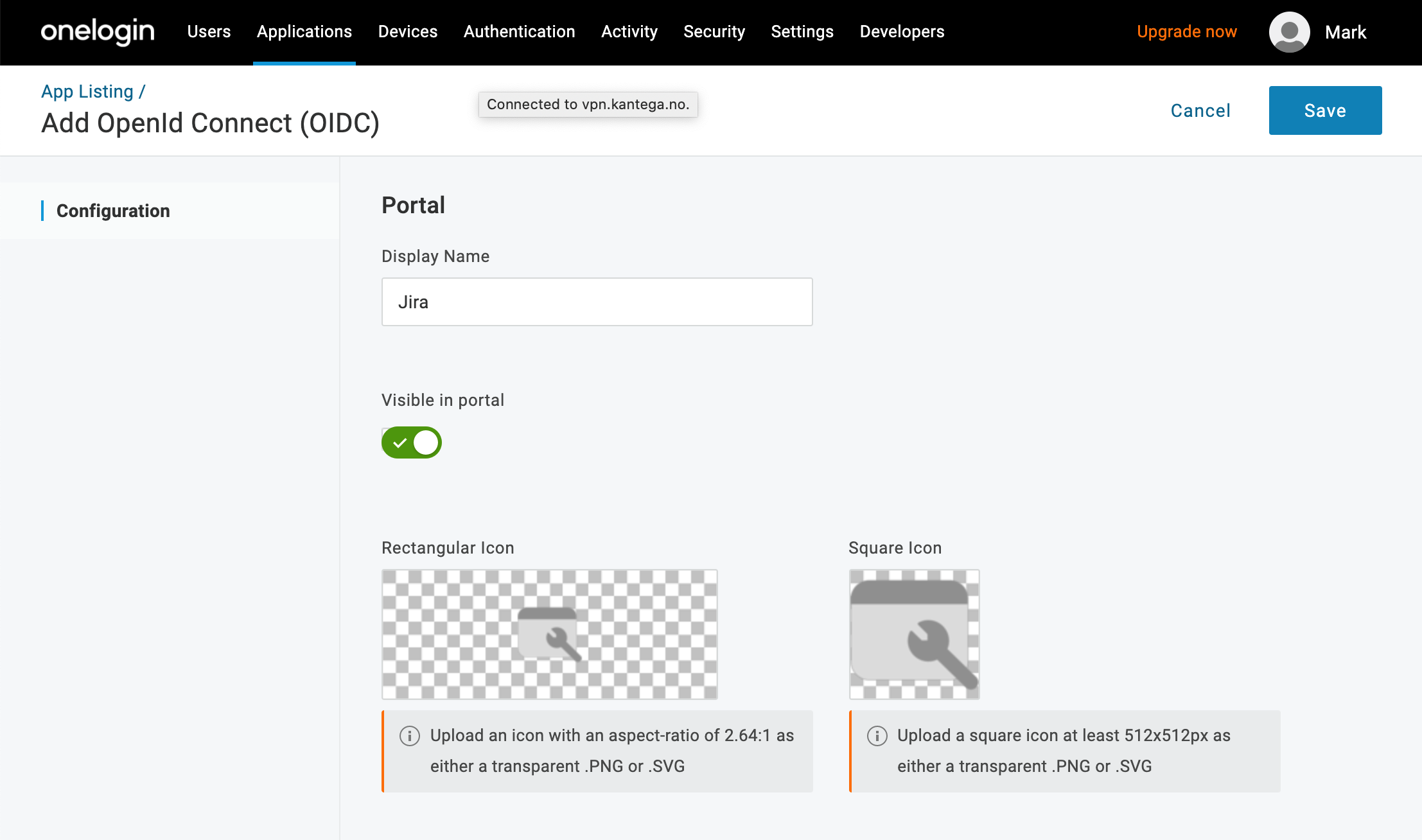
Give the app a Display Name, and click Save. Optionally, you can also give the app an icon and a textual description.
In the top menu item Users, Roles you may select what roles should have access to the new application.
You may also give single users access.
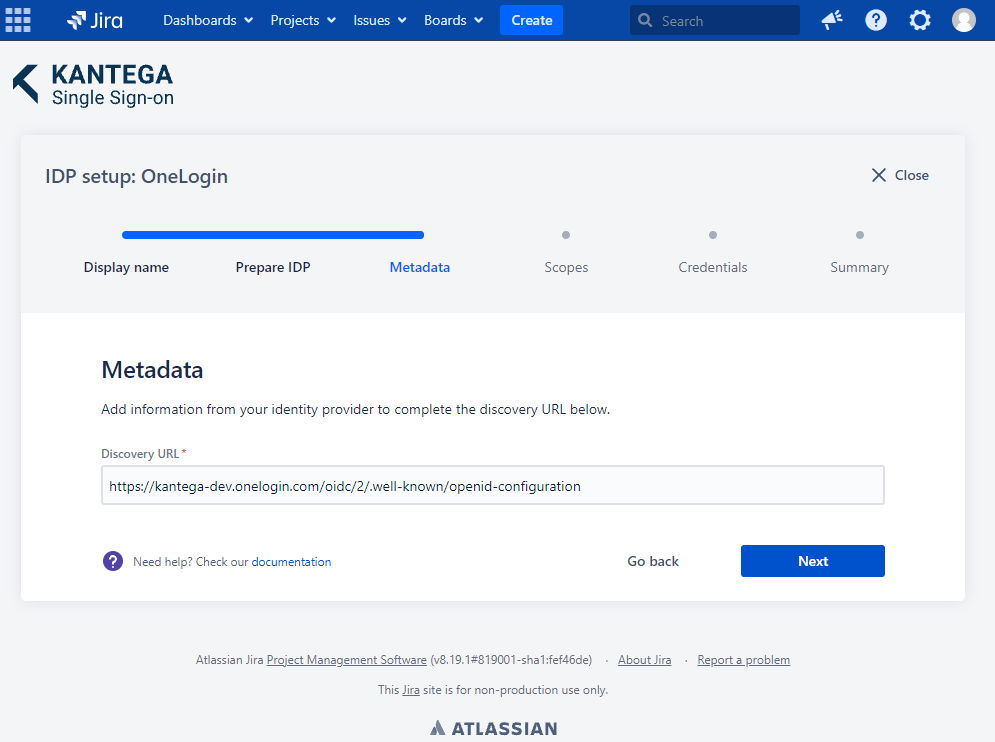
Go back to the Kantega SSO setup wizard.
I the Metadata step you replace {subdomain} to complete the Discovery URL.
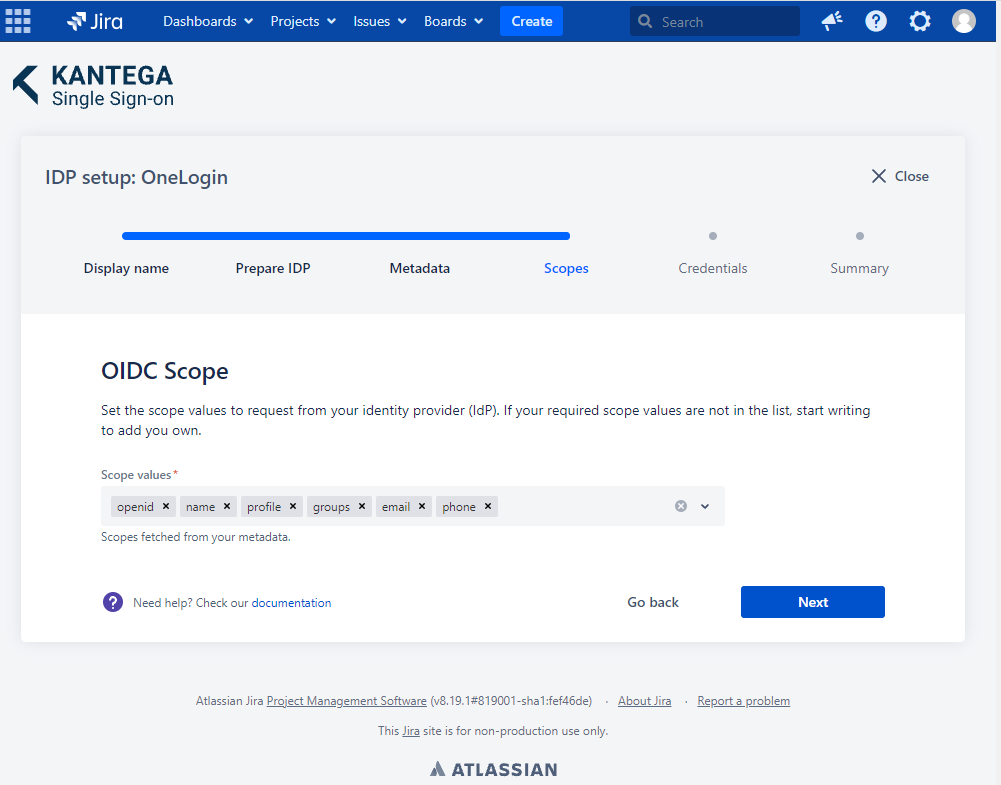
These are the scopes we were able to fetch from the metadata. You can add scope values from a list, start typing to add your own or unselect them. A minimum of one scope value is required.
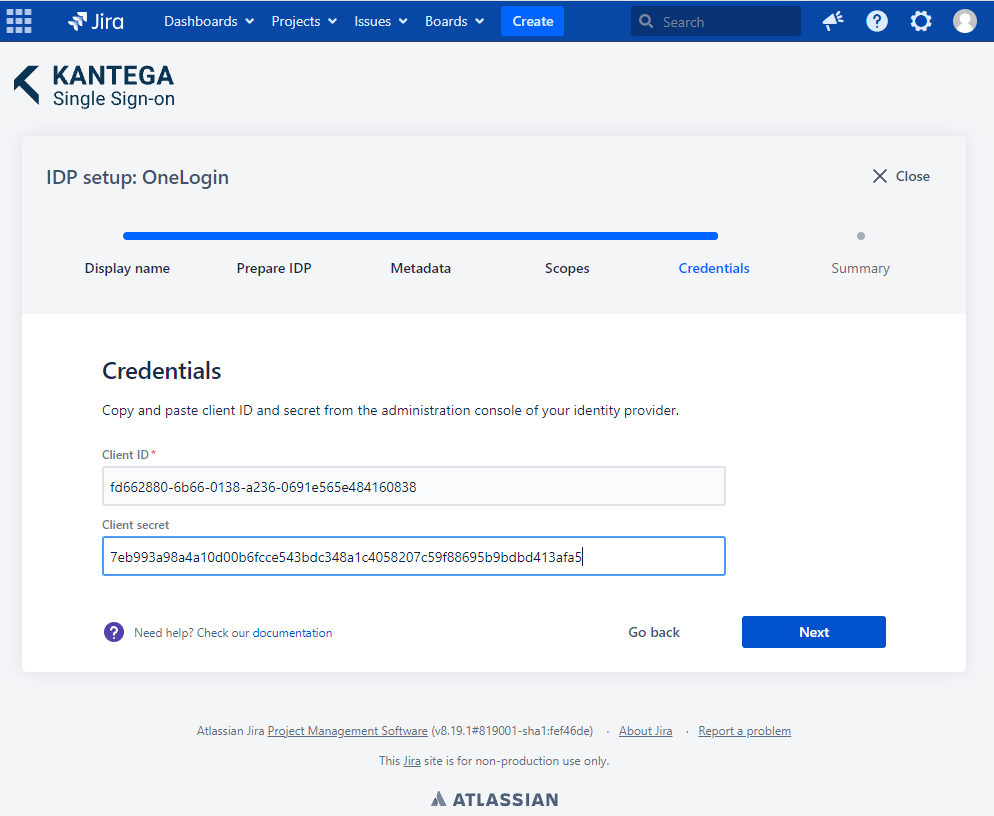
Insert client credentials from your Identity Provider. Client ID and Client secret are found in the SSO settings in Onelogin.
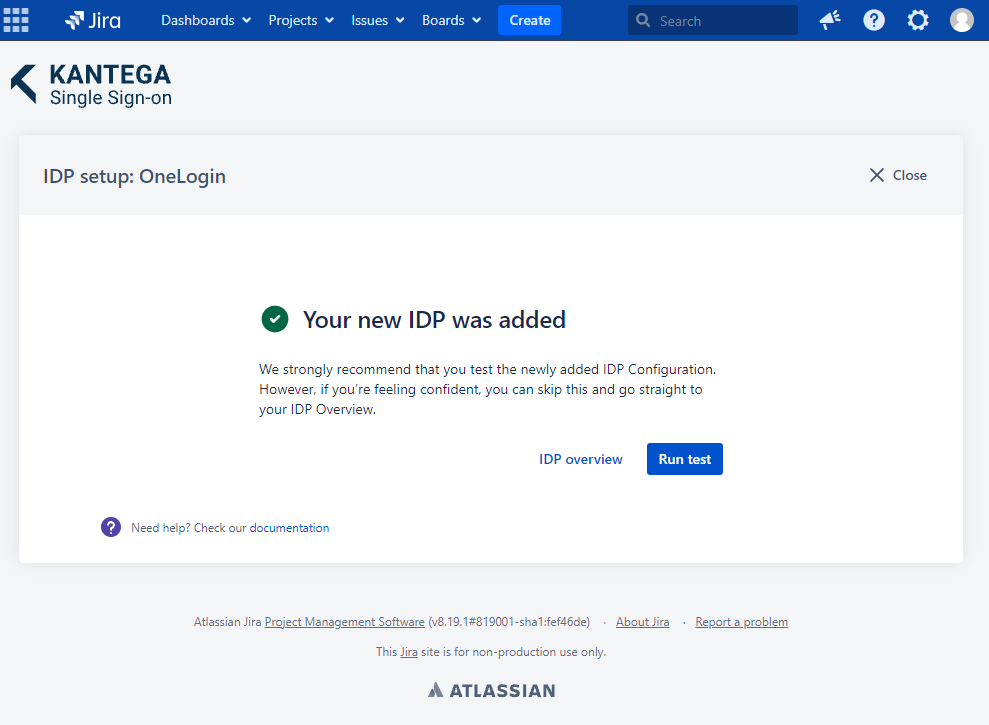
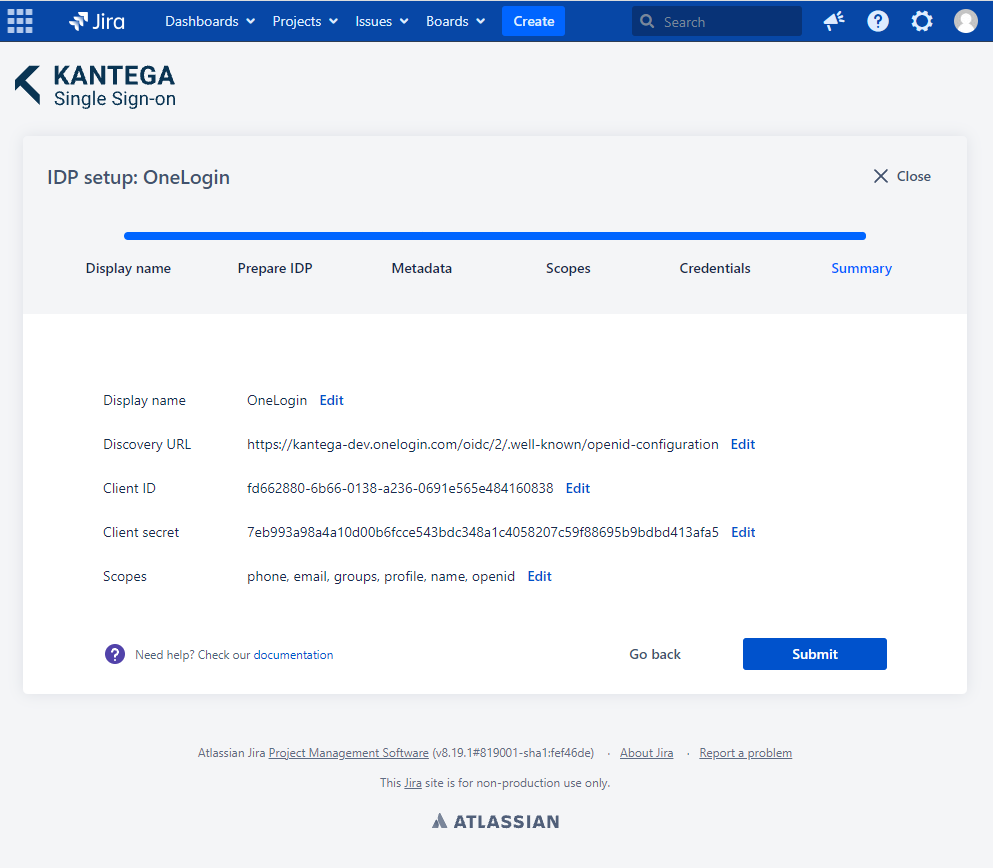
Check that everything looks good and submit your setup ![]()
Test that the log in with OneLogin works as expected. This will help identify if there are any issues with the configuration. Follow the steps to perform the login test.