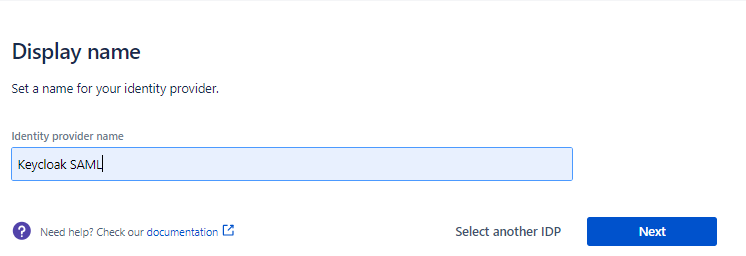
Choose a name for your identity provider. This is the user-facing name, so choose a name your users will recognize. This value can be changed later.
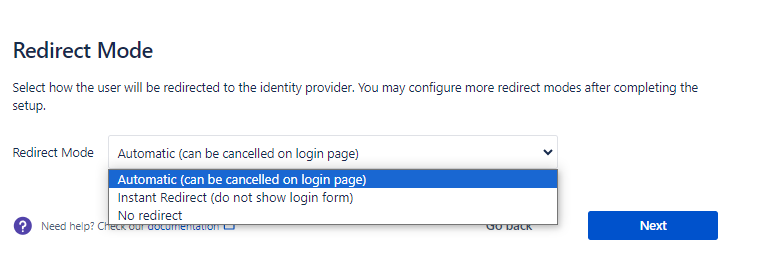
Select how the user will be redirected to the identity provider. You may configure more redirect modes after completing the setup.
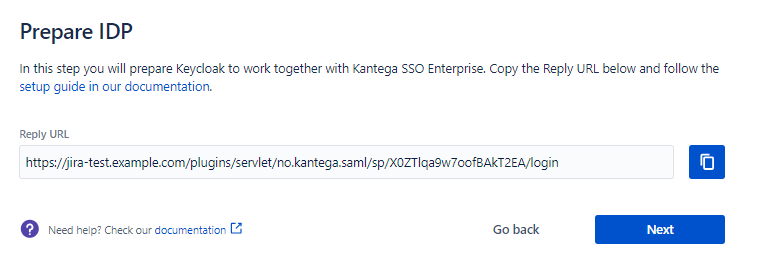
In this step, we will configure Keycloak to work with Kantega SSO. For this, you will need to copy the Reply URL provided. We will use this when setting up Keycloak.
If you are using SCIM with your provider, make sure to check out the documentation for configuring this before proceeding. It might be that you need to configure this first or at the same time as setting up SAML. |
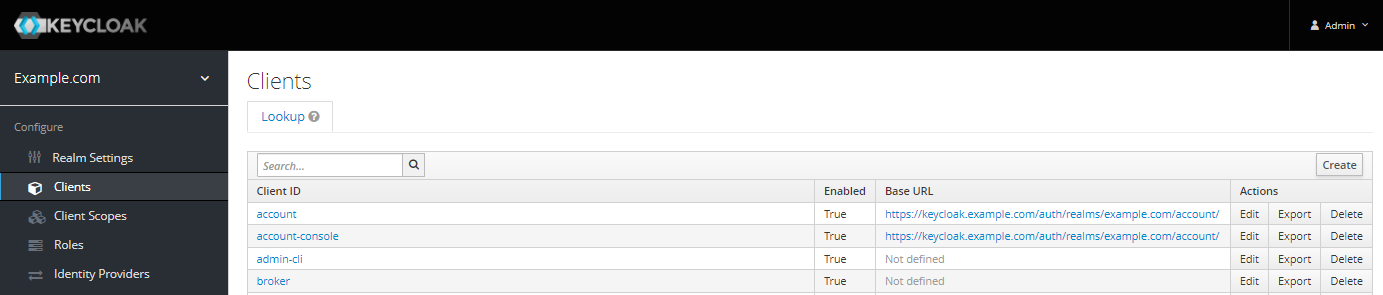
Sign in to the Keycloak admin console.
Select the correct realm (we are using http://example.com ) and then Create client.
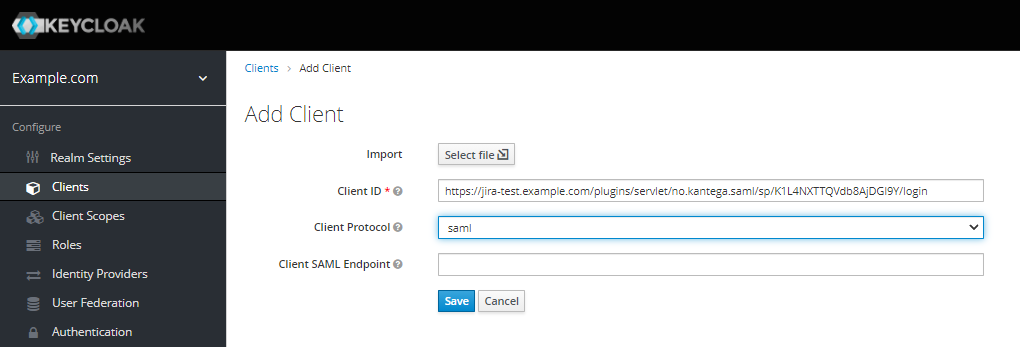
In Client ID, paste the Reply URL from the prepare step in the Kantega SSO wizard.
Select SAML as the Client Protocol and Save the client.
In Settings
Set Client Signature Required to Off
Paste the Reply URL into the following fields:
Valid Redirect URIs.
Master SAML Processing URL.
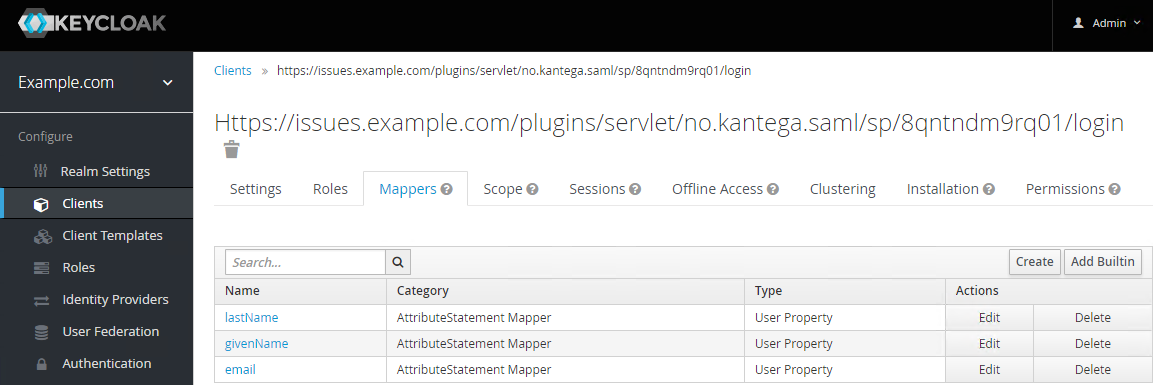
If you intend to use JIT provisioning to create user accounts the first time they log in, you will need to configure Mappers. Mappers make Keycloak include the requisite SAML Response attributes (email and name). If users already exist in JIRA (using LDAP or some other means of provisioning), you can skip this step.
Open the Mappers tab. We are going to add:
lastName
givenName
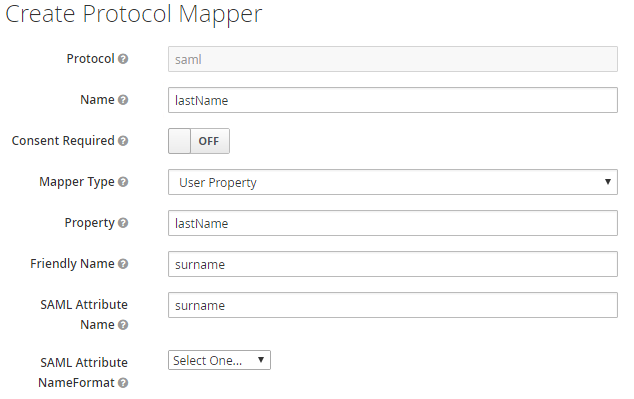
Create mapper for lastName:
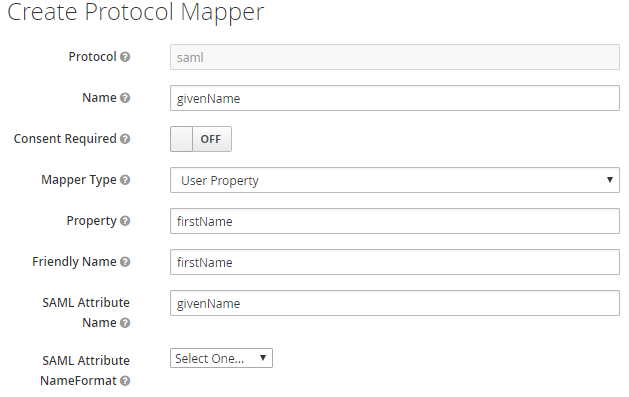
Create mapper for givenName:
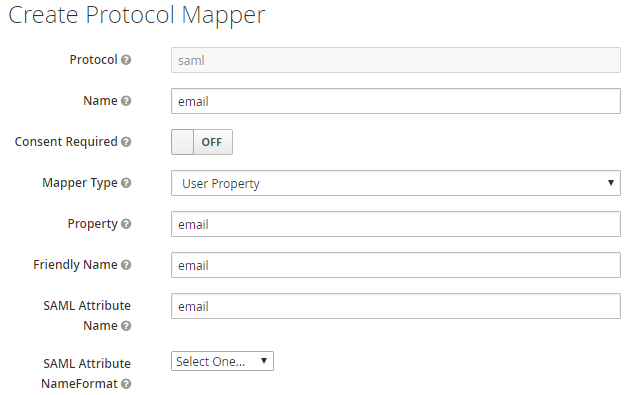
Create mapper for email:
If you intend to use Managed groups (manage your users' group meberships in Keycloak) or Auto create groups, you also need a mapper for group claims. If not, you can skip this step.
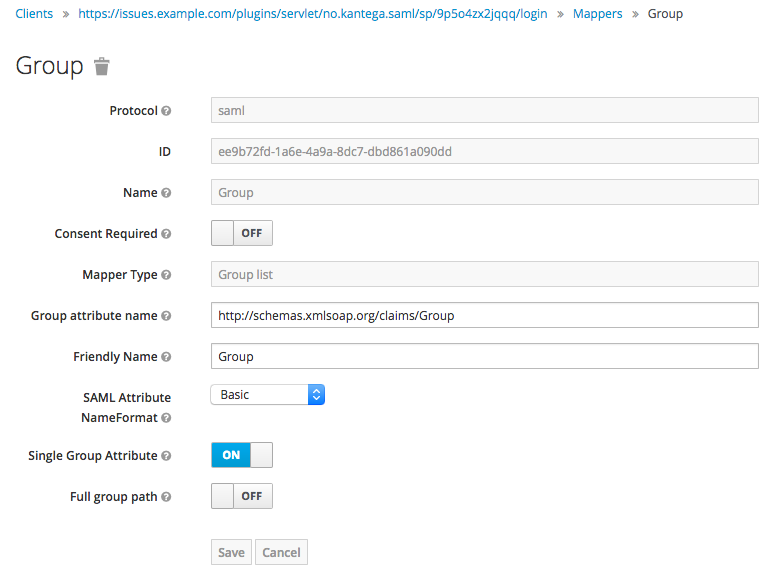
Create mapper for Group claims from identity provider (legacy, pre-5.3):
Set Name and Friendly Name to Group
Set Group attribute name to http://schemas.xmlsoap.org/claims/Group
Set Full group path to OFF
Go back to the Kantega SSO setup wizard, step 3 Metadata.
Provide the metadata URL (recommended):
https://<keycloak server>/auth/realms/<realm>/protocol/saml/descriptor
Substitute <keycloak server> with the DNS of your Keycloak server.
Substitute the realm identifier <realm> with your realm.
Alternatively, you can download the metadata file to disk and upload it in the KSSO wizard.
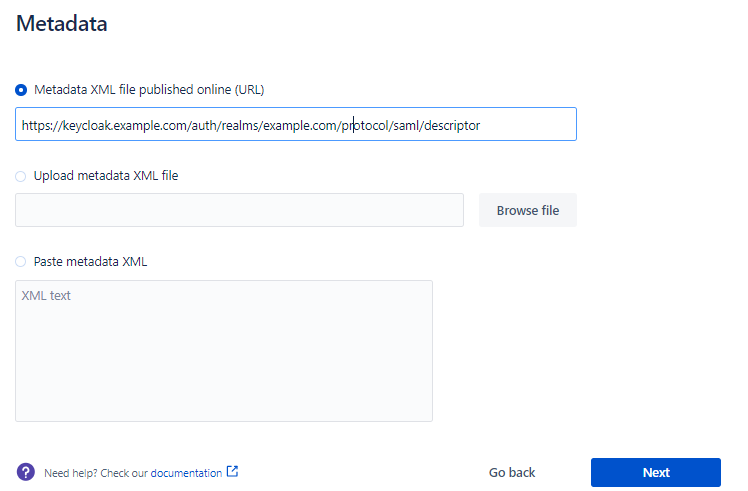
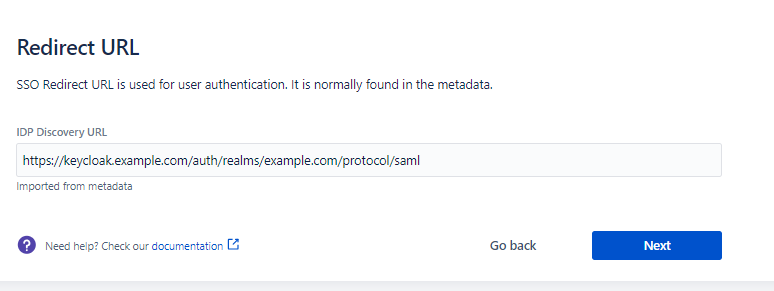
The Redirect URL is imported automatically from the metadata.
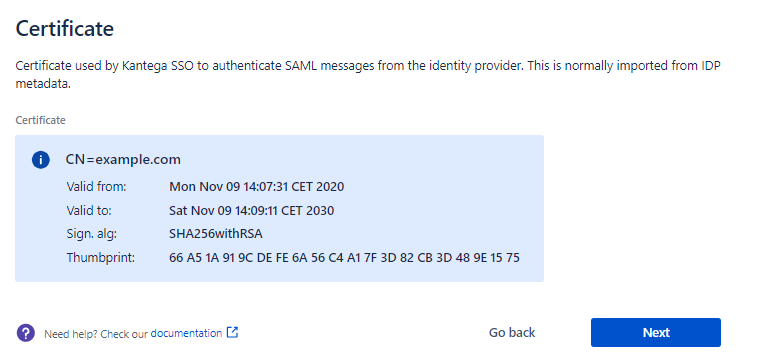
This step shows the certificate used to validate the SAML messages.
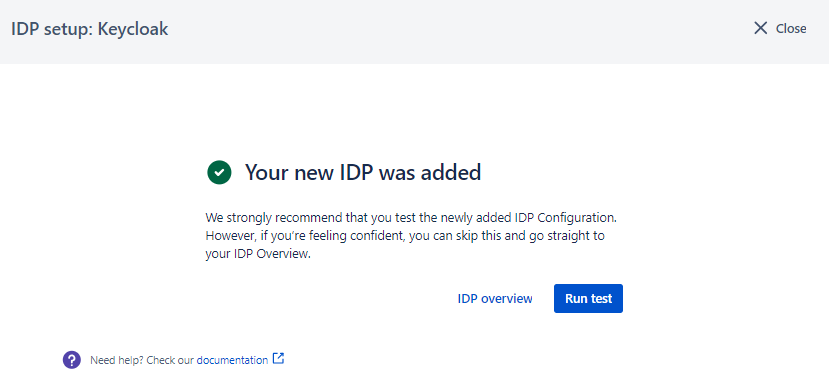
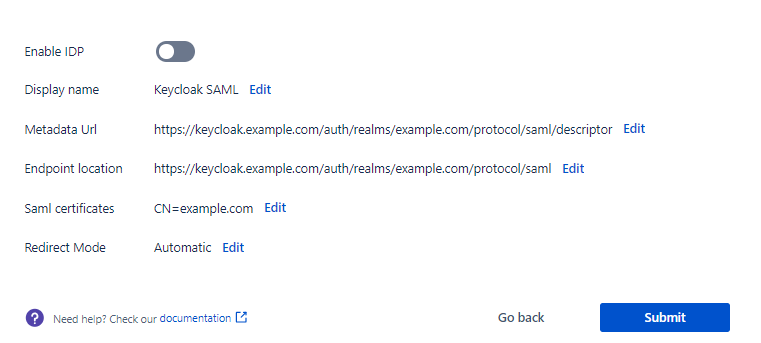
Check that everything looks good and submit your setup ![]()
Test that logging in with Keycloak works as expected. This will help identify if there are any issues with the configuration. Follow the steps to perform the login test.