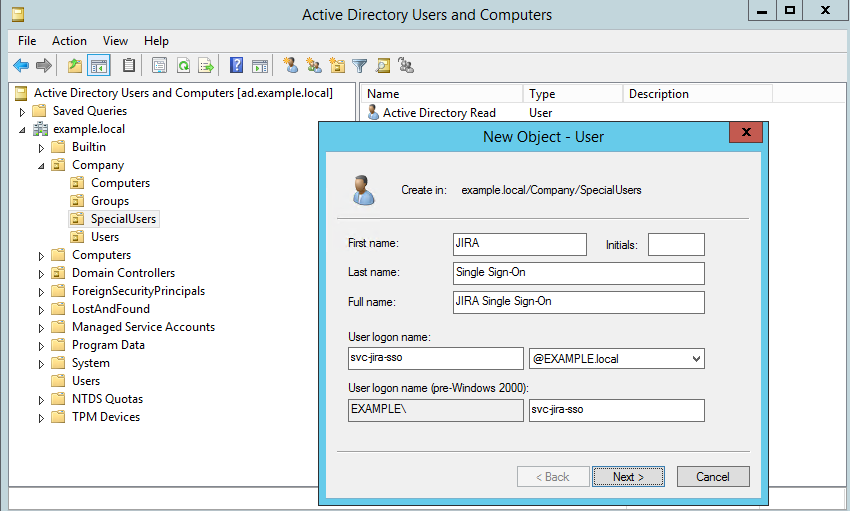
First, start with a new user object. We recommend using a dedicated user to map an SPN.
When running the ktpass-command, we need a user account to hold the SPN.
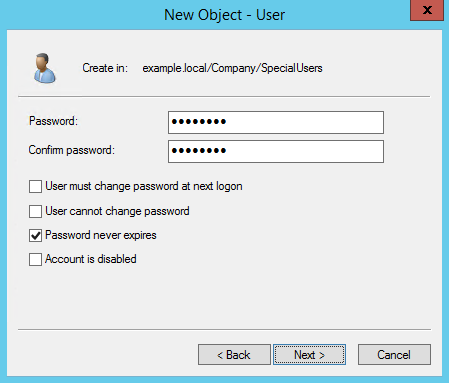
Make sure that the password never expires, and the user cannot change the password set.
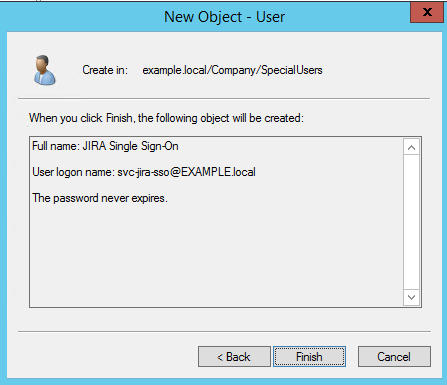
The details of the new user account.
Command / parameter |
| ||
|---|---|---|---|
| ktpass is included in windows 2008 onward and is located in C:\Windows\System32\ | ||
| HTTP - defines the protocol. HTTP (uppercase) is used regardless of accessing the site with https | ||
| Maps the Service Principal Name to an Active Directory user account. A unique account for each service should be created. The account should be configured with "Password never expires" and "User cannot change password" checked. | ||
/pass * | Some password. The password set replaces the user password. | ||
| The output location of the newly created keytab | ||
|
| ||
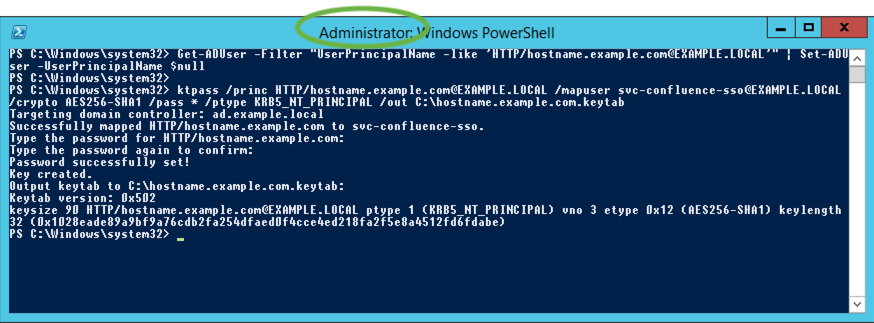
Get-ADUser command | The Get-ADUser command will set the requested UserPrincipalName potentially bound to another service acocunt to $null. This assures that the new keytab created will work even though the UserPrincipalName was bound to another account from before. It will not do any harm on a first time installation. |
Example command:
Get-ADUser -Filter "UserPrincipalName -like 'HTTP/issues.example.com@EXAMPLE.LOCAL'" | Set-ADUser -UserPrincipalName $null ktpass /princ HTTP/issues.example.com@EXAMPLE.LOCAL -mapuser EXAMPLE\svc-jira-sso -pass * /out C:\issues.example.com.keytab /ptype KRB5_NT_PRINCIPAL |
ktpass must be run in an elevated (administrator) PowerShell prompt as a user with domain or enterprise permissions.