1. Display name
Choose a name for your identity provider. This is the user-facing name, so choose a name your users will recognize. This value can be changed later.
...
2. Redirect Mode
Select how the user will be redirected to the identity provider. You may configure more redirect modes after completing the setup.
...
3. Prepare IDP
In this step, we will configure Azure AD Entra ID to work with Kantega SSO. For this, you will need to copy the Callback URL provided. We will use this when setting up Azure ADEntra ID.
...
Configure
...
Microsoft Entra ID
| Status | ||||
|---|---|---|---|---|
|
...
Sign in to the Azure Portal, navigate to Azure Active Directory Microsoft Entra ID > App registrations
Set up a new application. You can use our templates from the gallery by searching for “kantega” and follow the instructions.
...
The Redirect URL consists of two fields. Select "Web" in the left drop-down field and paste in the Callback URL from Kantega SSO in the right field.
Click the Register Register button in the bottom left of the page and wait a few seconds until the registration is finished.
...
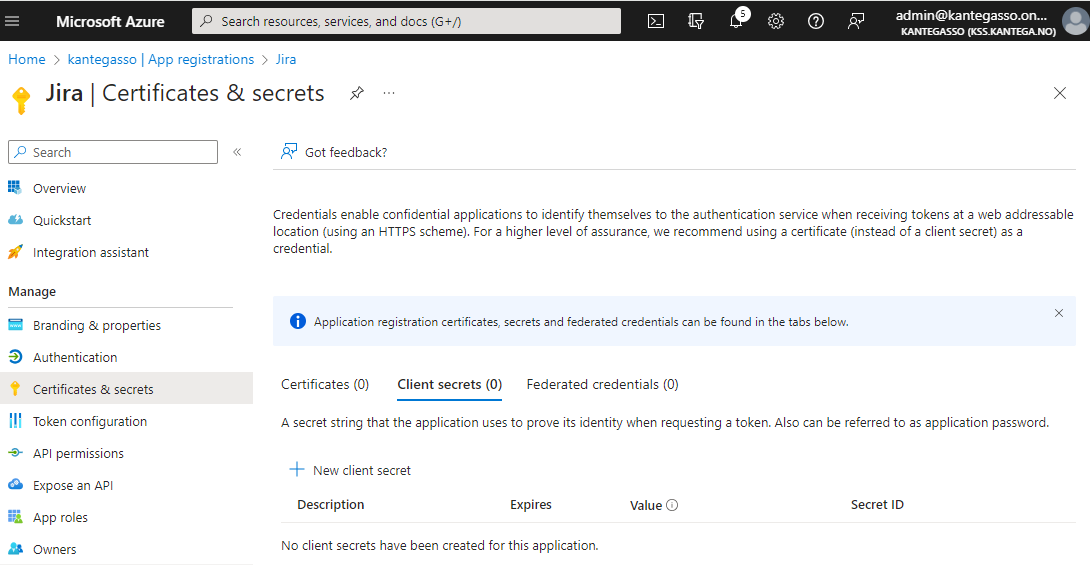
Copy the Directory (tenant) ID, Application ID and Client secret and go back to the Kantega SSO setup wizard , step 3 Metadata.
...
...
Go back to the Kantega SSO setup wizard.
...
4. Metadata
In the Metadata step, paste the Directory (tenant) ID from clipboard into Tenant ID. The IDP Discovery URL is generated from default URL and tenant ID. Custom URL’s can also be inserted here.
...
...
5. Scopes
These are the scopes we were able to fetch from the metadata. You can add scope values from a list, start typing to add your own or unselect them. A minimum of one scope value is required.
...
...
6. Credentials
In this step, you need to insert client credentials from Azure ADEntra ID. Paste the Application (client) ID and the Client secret value you copied from Azure AD Entra ID into the respective fields.
...
7. Token configuration
You might want to configure some more claims for your ID tokens sent from Entra ID. If you want to test the default setup, simply skip this step.
One claim that might not come by default in your tenant is the email claim, which is a required attribute to create a user in Jira with Just-in-time user provisioning. To add the email claim, navigate to Token Configuration in your App Registration > Add Optional Claim.
...
...
Select ID, and check the email claim checkbox:
...
8. Summary
Check that everything looks good and submit your setup ![]()
...
Test
Test that logging in with Azure AD Entra ID works as expected. This will help identify if there are any issues with the configuration. Follow the steps to perform the login test.
...
...
During the first login on an App Registration, you will be prompted to give consent for the integrated Atlassian application to read user data. If your organization has activated that admin consent is required for logins, your Azure AD administrator will have to consent on behalf of the organization, under App Registrations > your app > API permissions:
...
Optional: Get group claims for user
Follow this guide to get group claims for user in the OIDC login:
https://kantega-sso.atlassian.net/wiki/x/K4FCEg
Optional: Get sAMAccountName from OIDC login
This may be done in the exact same way as described for SAML here: